Application program operation method and device
A technology of application programs and operation methods, applied in the computer field, can solve problems such as the inability to guarantee the security of users' personal information, threats to application program operation security, etc., and achieve the effect of improving operation security and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
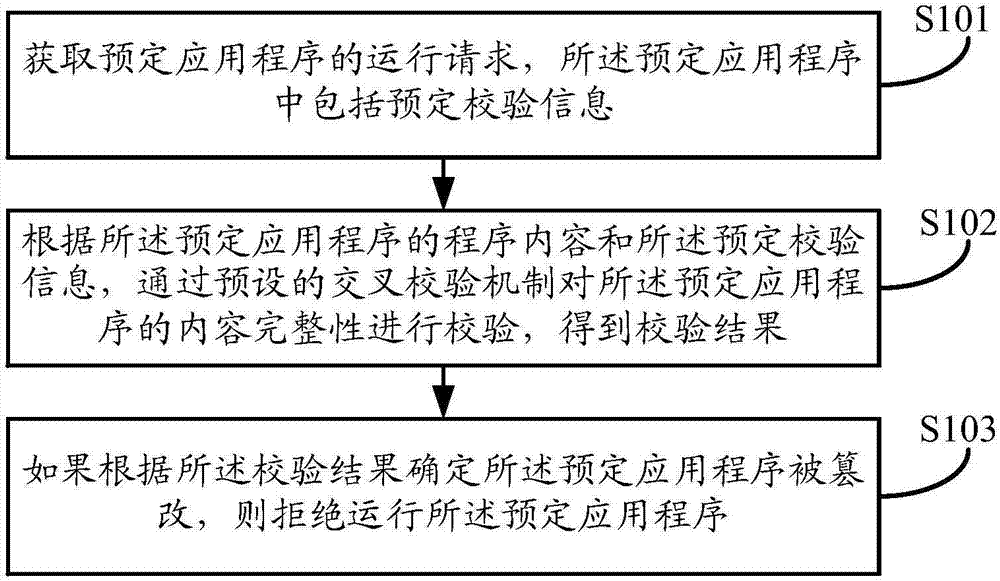
[0050] Such as figure 1As shown, the embodiment of the present application provides a method for running an application program. The execution body of the method may be a terminal device, and the terminal device may be a personal computer, a mobile phone, or a tablet computer. The method can be applied to determine whether the application program has been tampered with, and to prevent the personal information from being stolen by the user using the tampered application program. The method may specifically include the following steps:
[0051] In step S101, an operation instruction of a predetermined application program is acquired, and the predetermined application program includes predetermined verification information.
[0052] Wherein, the predetermined application program can be any application program, such as an application program based on the Android (i.e. Android) operating system, or an application program based on the iOS operating system, such as an instant messagi...
Embodiment 2
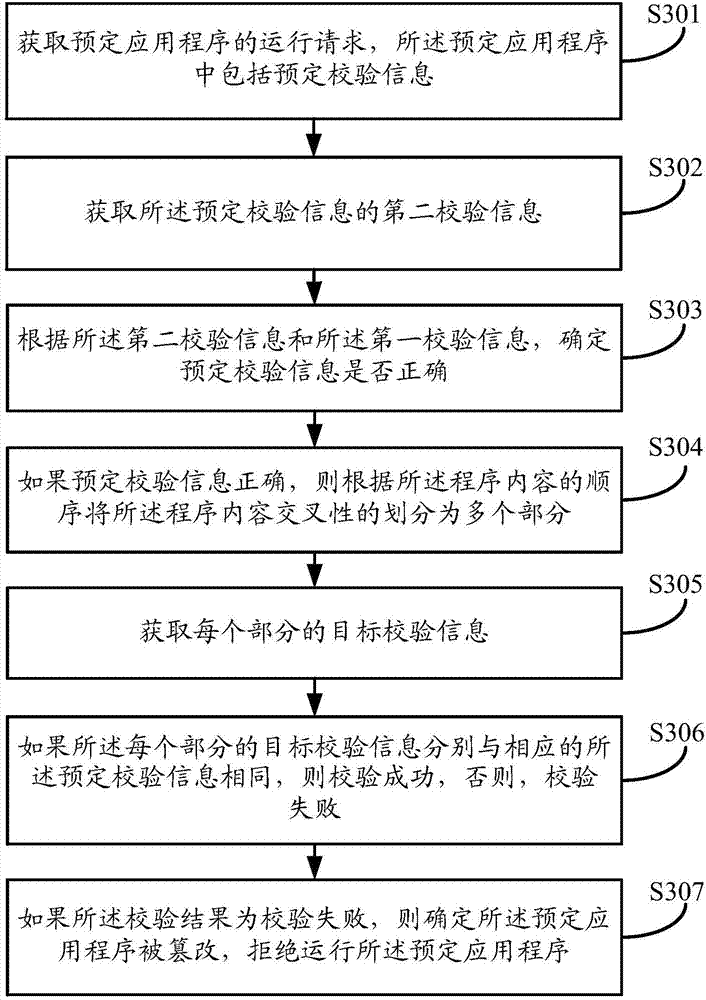
[0062] Such as image 3 As shown, the embodiment of the present application provides a method for running an application program. The execution subject of the method may be a terminal device, where the terminal device may be a personal computer, a mobile phone, or a tablet computer. The method can be applied to determine whether the application program has been tampered with, and to prevent the personal information from being stolen by the user using the tampered application program. The method may specifically include the following steps:
[0063] In step S301, an operation instruction of a predetermined application program is obtained, and the predetermined application program includes predetermined verification information.
[0064] Among them, in order to ensure the security of the reservation verification information in the reservation application program and prevent users from arbitrarily changing its relevant content, causing the subsequent verification process to lose ...
Embodiment 3
[0082] The above is the running method of the application program provided by the embodiment of the present application. Based on the same idea, the embodiment of the present application also provides a device for running the application program, such as Figure 5 shown.
[0083] The running device of the application program includes: an instruction acquisition module 501, a verification result determination module 502 and a refusal to run module 503, wherein:
[0084] An instruction obtaining module 501, configured to obtain an operation instruction of a predetermined application program, wherein the predetermined application program includes predetermined verification information;
[0085] The verification result determination module 502 is configured to verify the content integrity of the predetermined application program through a preset cross-check mechanism according to the program content of the predetermined application program and the predetermined verification inform...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com