Method for evaluating vulnerability node of electric cyber-physical system based on undetectable information attack pre-warning technology
A technology for information attack and information detection, applied in transmission systems, digital transmission systems, electrical components, etc., to achieve the effect of comprehensive technical framework, enhanced protection, and safe and stable operation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The technical solution of the present invention will be described in detail below according to the accompanying drawings, and the purpose and effect of the present invention will become more obvious.
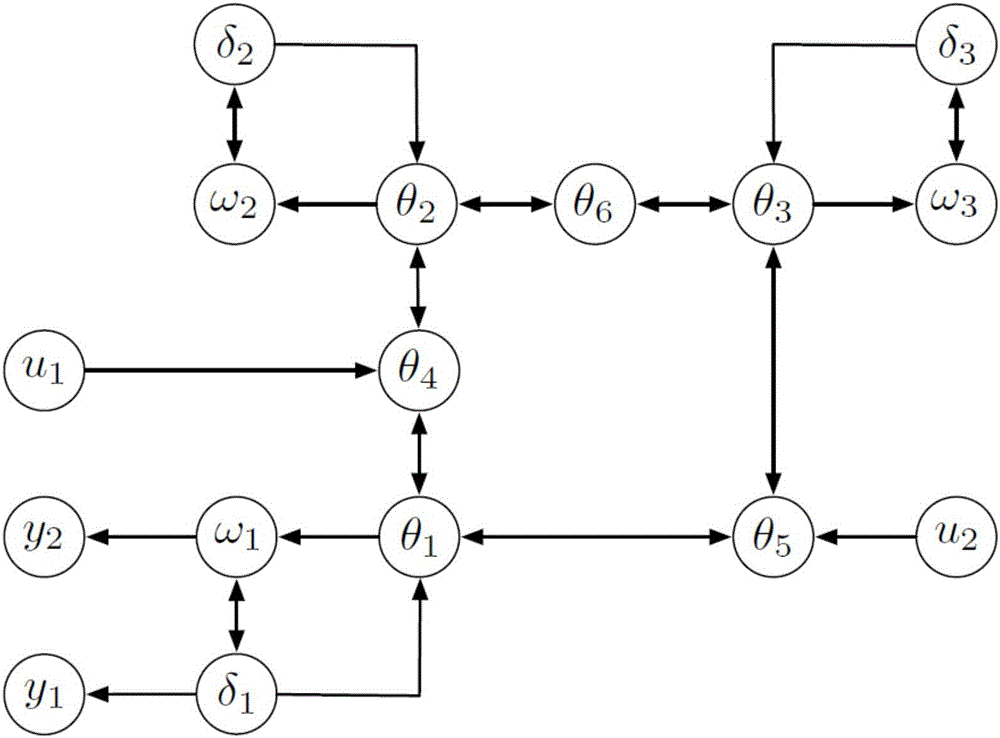
[0041] figure 1It is topology of IEEE 3-machine 6-node system. Through this example, the object of the present invention can be better explained. figure 1 There are three generators in :
[0042] (1)w 1 ,w 2 ,w 3 is the rotation frequency;
[0043] (2)δ 1 ,δ 2 ,δ 3 for the corner;
[0044] (3) θ 1 ,...,θ 6 is the phase angle that may be attacked;
[0045] (4) System u 1 , u 2 for simulated attacks;
[0046] (5) output y 1 ,y 2 Used to observe attacks and identify potentially undetectable nodes.
[0047] Such as figure 1 As shown, add the input (attack) u 1 Used to judge node θ 4 Whether it is a vulnerable node, similarly u 2 Used to judge node θ 5 Whether it is a vulnerable node. when u 1 , u 2 , the method of the present invention is used to jud...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com