Password operation realization method and device based on encryption card and server
An implementation method and server technology, applied in the field of cryptographic operations, can solve the performance limitations of a single encryption card, low product performance, complex processes, etc., and achieve the effects of fast and convenient cryptographic operation efficiency, excellent performance, and low cost
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0046] Embodiments of the present invention provide a method and device for implementing high-performance cryptographic operations, so as to provide efficient cryptographic services such as signature verification based on encryption card hardware and server CPU (Central Processing Unit, central processing unit) and other hardware resources. This method has the characteristics of low hardware cost, fast computing speed and excellent expansibility.
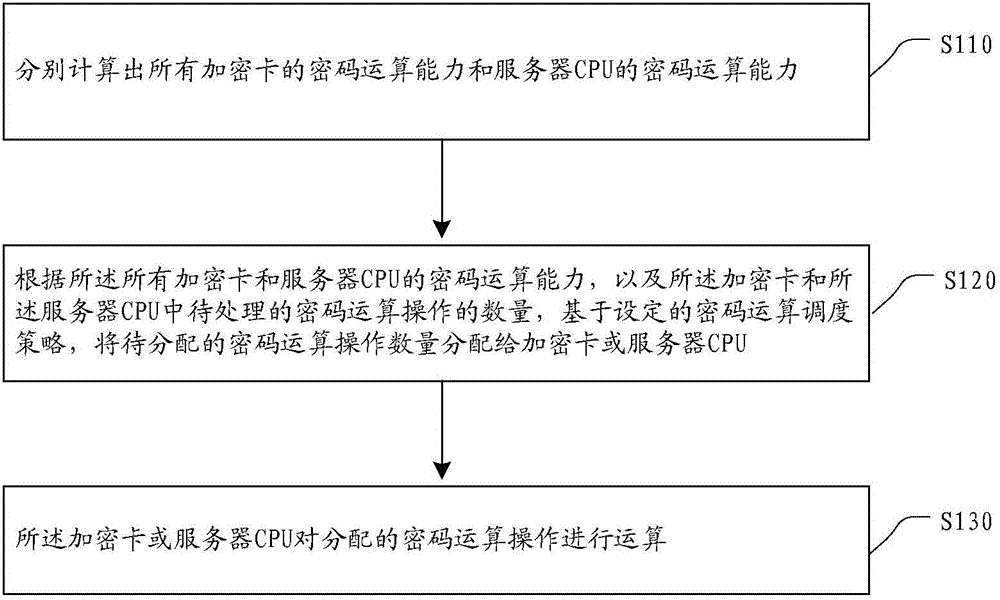
[0047] This embodiment provides a processing flow for implementing a cryptographic operation based on an encryption card and a server, as follows: figure 1 As shown, the following processing steps are included:
[0048] Step S110, respectively calculating the cryptographic computing capabilities of all encryption cards and the cryptographic computing capabilities of the server CPU.
[0049] Obtain how many encryption cards are currently used for cryptographic hardware operations, perform cryptographic operations for a set number of...
Embodiment 2
[0064] This embodiment provides a device for implementing cryptographic operations based on an encryption card and a server, and its specific implementation structure is as follows: figure 2 As shown, it can specifically include the following modules:
[0065] The cryptographic computing capability calculation module 21 is used to calculate the cryptographic computing capabilities of all encryption cards and the cryptographic computing capability of the server CPU respectively;
[0066] The cryptographic operation allocation module 22 is configured to base on the set cryptographic operation scheduling according to the cryptographic computing capabilities of all the encryption cards and the server CPU, and the number of cryptographic operations to be processed in the encryption cards and the server CPU Strategy, assigning the number of cryptographic operations to be allocated to the encryption card or server CPU;
[0067] The cryptographic operation processing module 23 is co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com