Terminal authentication method and device used in mobile communication system
A mobile communication system and terminal authentication technology, applied in the field of terminal authentication methods and devices, can solve the problem of SIM card restricting the development of thin and light terminals, and achieve the effect of facilitating the development of thin and light terminals
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
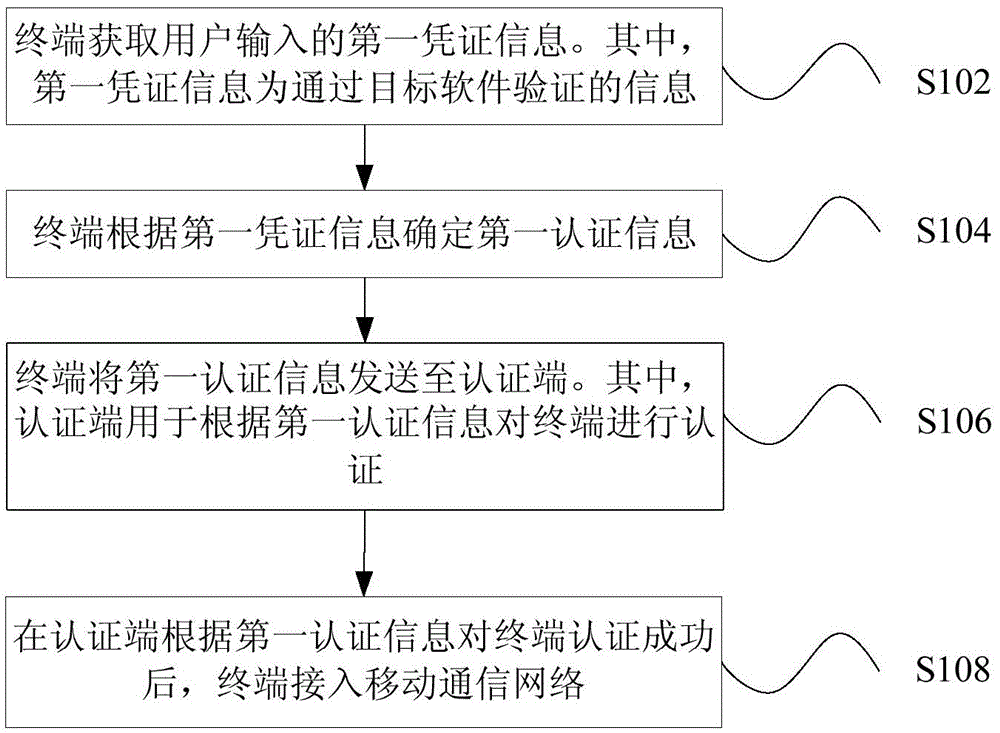
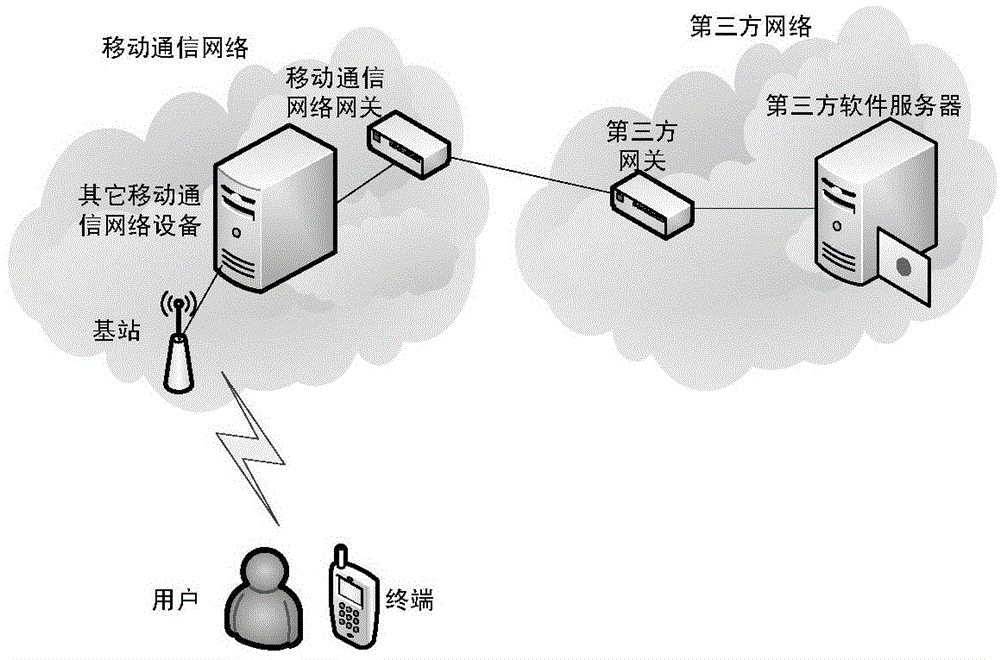
[0101] First, the terminal determines identification data according to the first credential information.
[0102] Then, the terminal generates first authentication information according to the identification data.
[0103]Specifically, the terminal side may include an identification data generation device, the identification data generation device is used to generate corresponding identification data according to the first credential information input by the user, and the identification data is used to generate authentication information through the terminal authentication information generation device, such as Figure 4 shown.
[0104] Since the format of the credential information that can be used to authenticate the target software designed by a third party is irregular, for example, the credential information can be an email address, a string of digital symbols, etc., while in communication authentication, the identification data needs to have a fixed format, for example, ...
example 2
[0110] First, the terminal receives an authentication request including a random number sent by the authenticator.
[0111] Wherein, this step may be performed before the aforementioned step S102.
[0112] Then, the terminal determines first authentication information according to the first credential information and the random number.
[0113] Wherein, for the safety of network transmission, the authentication information request sent by the mobile communication network to the terminal may include a random number, and the terminal may use the first authentication function to determine the authentication information according to the random number and the first credential information input by the user, and Send the authentication information to the mobile communication network, such as Figure 5 As shown, the first authentication function is implemented in the device for generating terminal authentication information. The mobile communication network side has the information ...
example 3
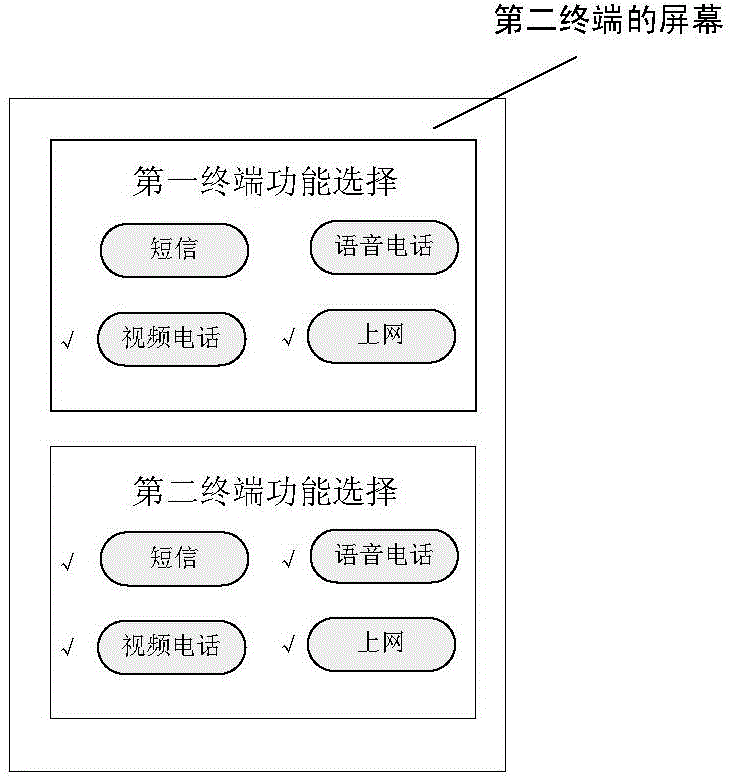
[0210] The first determining unit 20 may include: a determining module and a generating module. The determining module can be used to make the terminal determine the identification data according to the first credential information; and the generating module can be used to make the terminal generate the first authentication information according to the identification data. Specifically, the terminal side may include an identification data generation device, the identification data generation device is used to generate corresponding identification data according to the first credential information input by the user, and the identification data is used to generate authentication information through the terminal authentication information generation device. The detailed introduction of the content is the same as the aforementioned method part, and will not be repeated here.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com