A database protection method
A database and data technology, applied in the direction of electrical digital data processing, special data processing applications, instruments, etc., can solve the problems that cannot fundamentally prevent data leakage in the database, database data information leakage, leakage, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
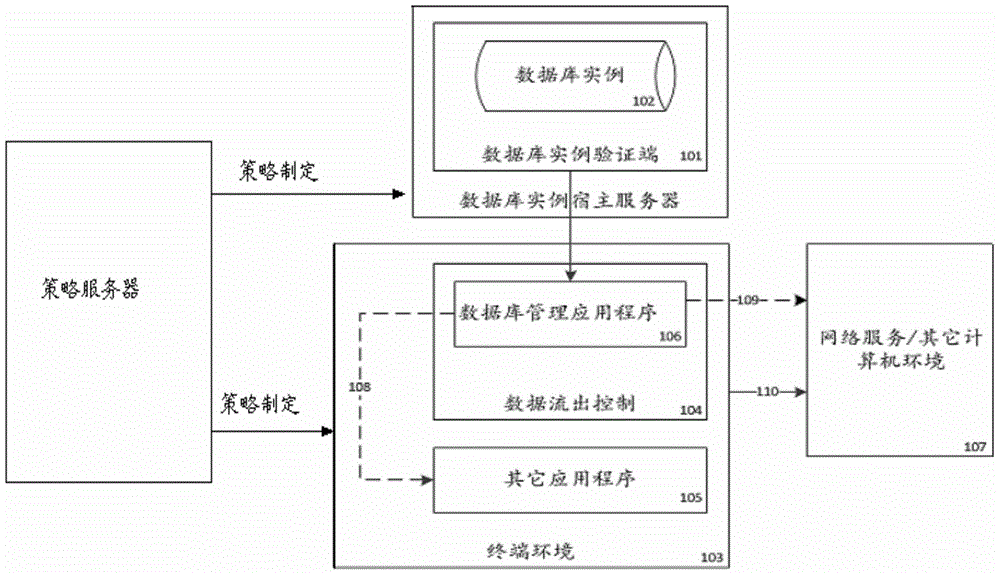
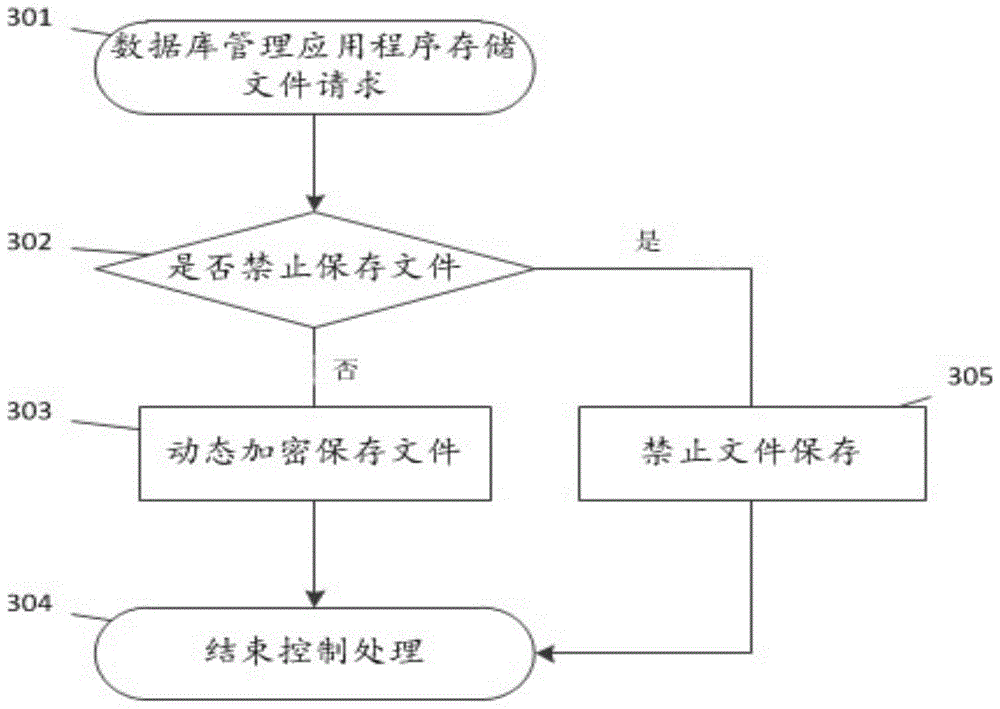
[0026] In order to make the objects and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and examples of implementation.
[0027] The main purpose of the present invention is to control the loss of data information after the database terminal management program obtains the protected database instance, so as to ensure the safety of the data information in the database in the terminal environment.
[0028] In the following detailed description, numerous specific details are given, such as specific method sequences, structures, elements, and connections. It should be understood, however, that this and other specific details such as: common knowledge, system environment elements, etc., are not exhaustive.
[0029] 1) Strategy formulation and application;
[0030] The policy is uniformly formulated and delivered by the policy server; the policy server is responsible for formul...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com