API (application programming interface) monitoring method and device
A monitoring interface and processing method technology, applied in computer security devices, instruments, digital data authentication, etc., can solve problems that users ignore, hidden dangers of smart mobile terminals, etc., and achieve the effect of improving the safety of use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
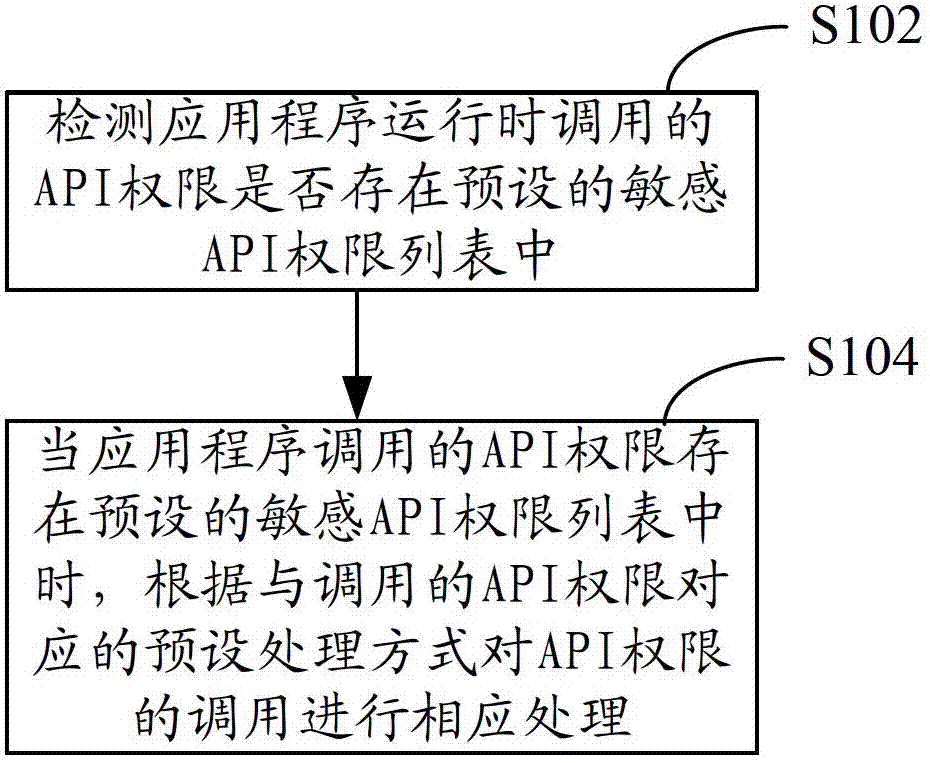
[0023] Such as figure 1 Shown, in one embodiment, a kind of API monitoring method comprises the following steps:
[0024] Step S102, detecting whether the API permission invoked by the application program is in the preset sensitive API permission list.
[0025] Sensitive API permissions refer to the APIs called when the application is installed or running to implement some functions that involve privacy information, such as reading call records, reading geographic location information, monitoring user calls, modifying system files, etc. If the application program calls sensitive APIs to implement these functions, it will bring great security risks to the smart mobile terminal. Specifically, APIs used to implement these privacy functions are recorded in the sensitive API permission list.
[0026] Step S104, when the API permission invoked by the application program exists in the preset sensitive API permission list, corresponding processing is performed on the call of the API...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com