Biological key and biological lock
A biological and key technology, applied in the field of biological locks, can solve the problems of easy interception and counterfeiting of remote control signals, and achieve the effects of preventing counterfeiting and counterfeiting, being convenient to carry and use.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
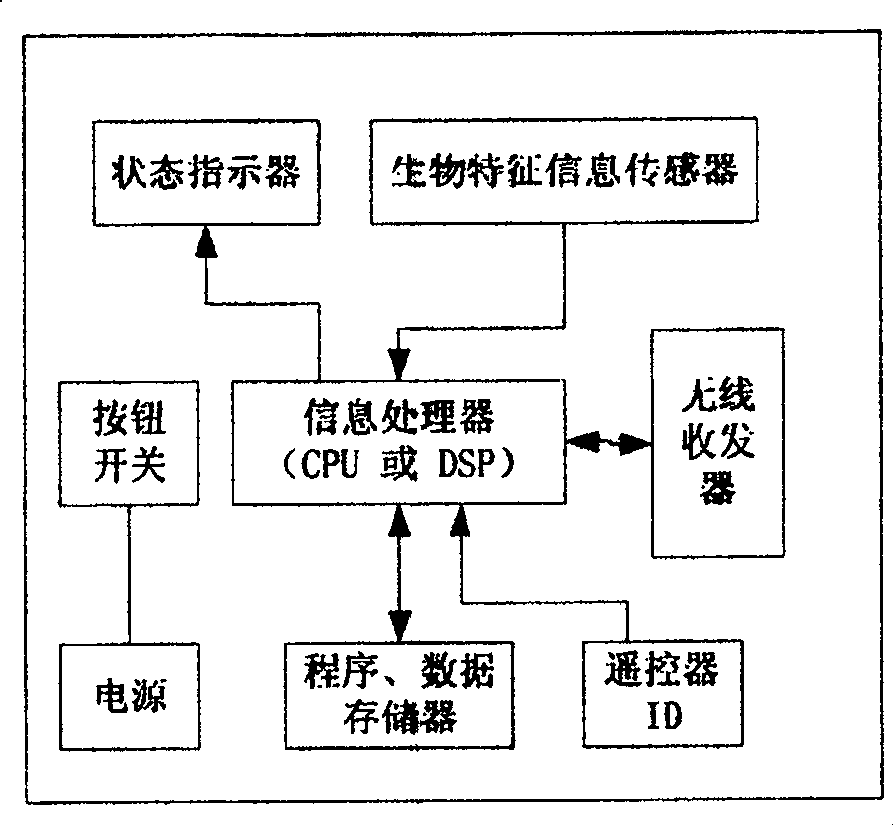
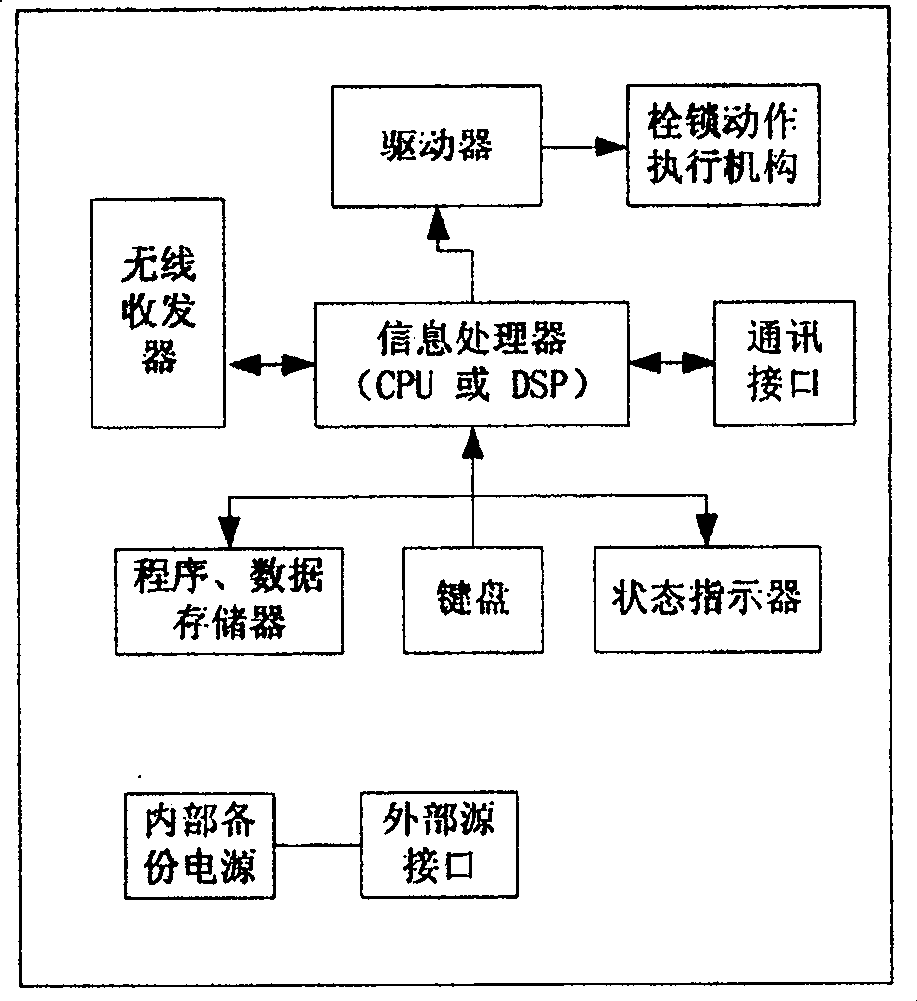
[0016] Embodiment 1: with reference to attached Figure 1~3 . Biometric key and biometric lock. The biometric key has built-in biometric information and transmits it to the biometric lock wirelessly. , the biological lock is opened, if it does not match, the biological lock cannot be opened. The biological key contains sensors, information processors, program data storage, wireless transceivers, power supplies and button switches that contain human biometric information. The biological information collected by the biometric information sensors is sent to the information processor, and the program data storage is temporarily stored from information processing The information of the device, the information of the identification code ID of the biological key to the information processor, the wireless transceiver is used to receive the information sent by the information processor, or the information sent by the biological lock, the button switch controls the work of the biologic...
Embodiment 2
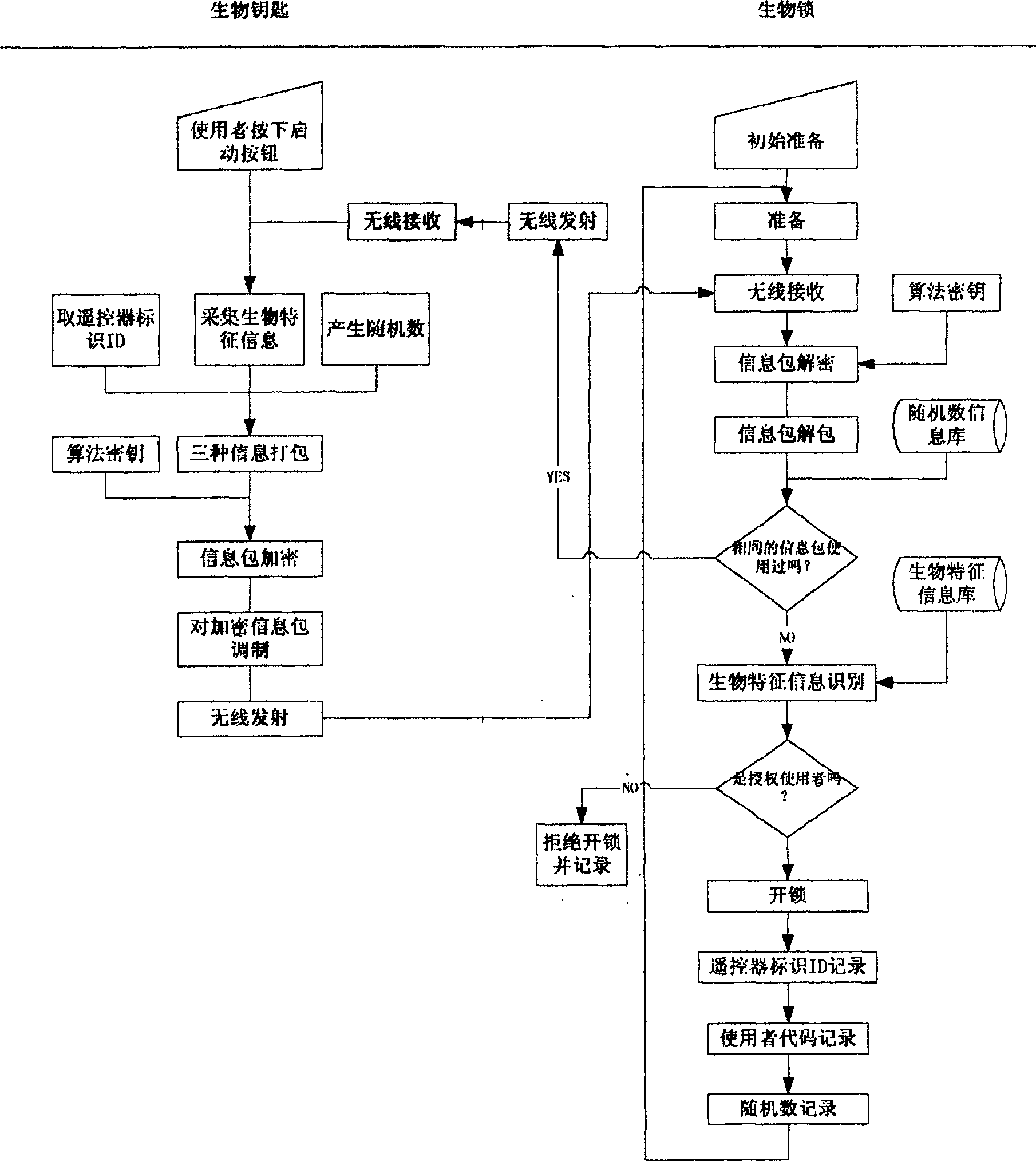
[0019] Embodiment 2: with reference to attached image 3 and 4. The working method of the bio-key and bio-lock, ① The biometric information collected by the bio-key and the information in it are encrypted and transmitted to the matching bio-lock, and the bio-lock performs the biometric information received and the information in the bio-key. Identify and judge, "legal" biological locks are automatically opened, and "illegal" biological locks refuse to unlock. ② The biometric information collected by the biometric key and its unique ID that is different from other identification codes are automatically encrypted and sent to the matching biometric lock. The biometric lock decrypts and unpacks the received biometric information. After judging the legality of the information, identifying the biometric information, identifying the identification code ID, and judging the validity of the information, an unlock instruction is issued and the lock is opened; otherwise, the unlock is re...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com