Method, system and apparatus for maintaining user privacy in knowledge interchange system
A user-friendly and private technology, applied in computer security devices, special data processing applications, instruments, etc., can solve problems such as worsening problems and fewer experts
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
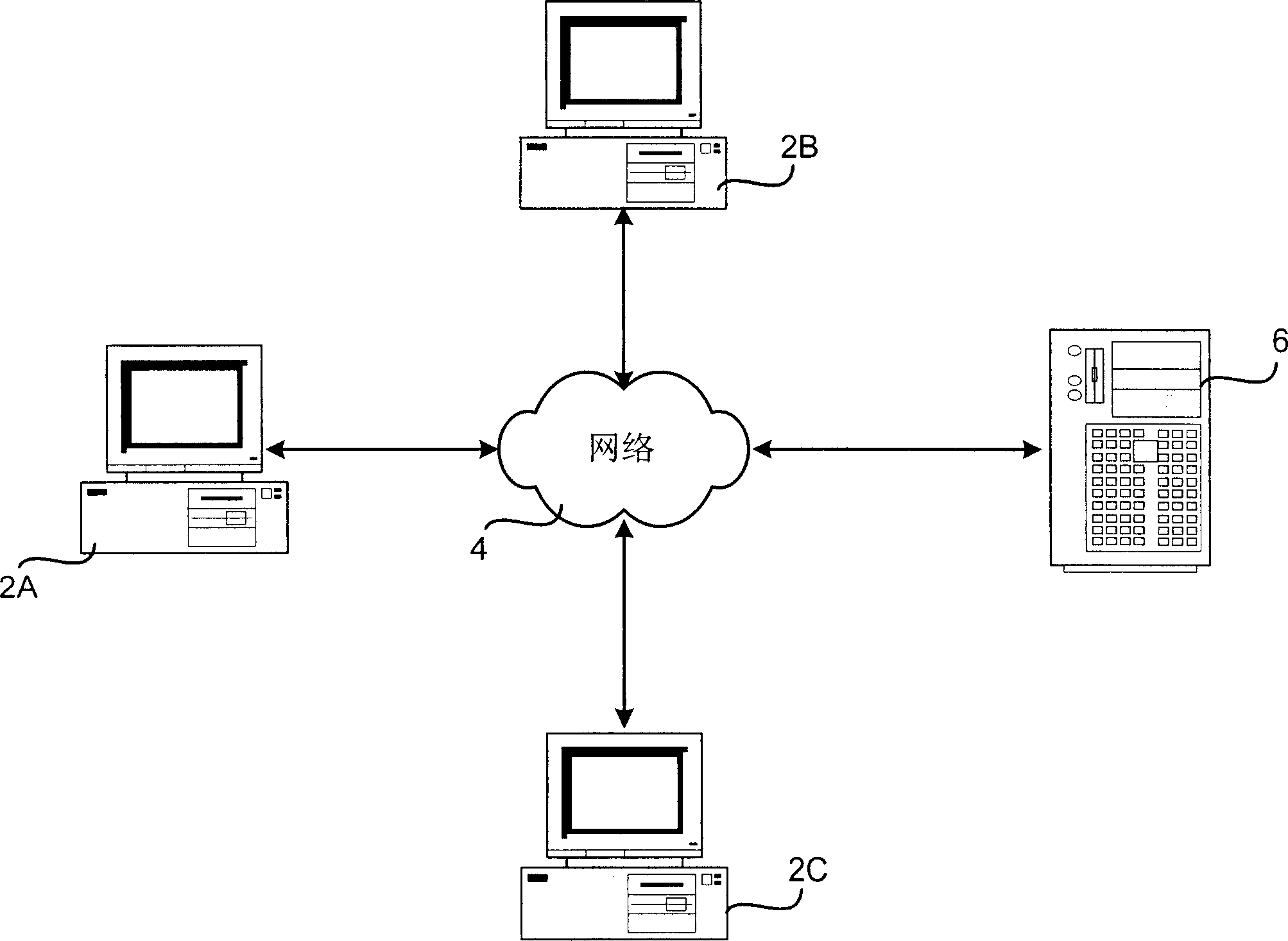
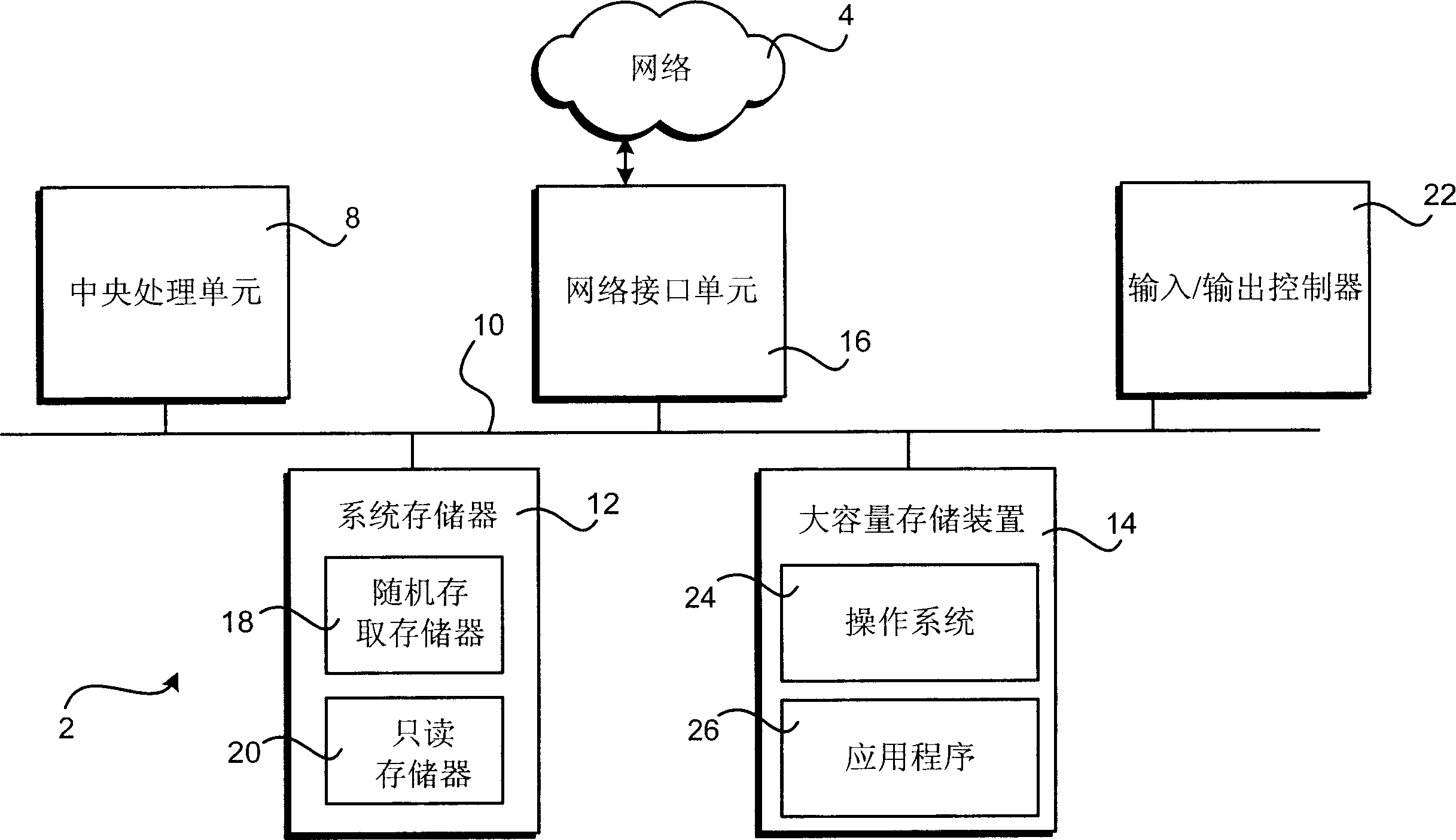
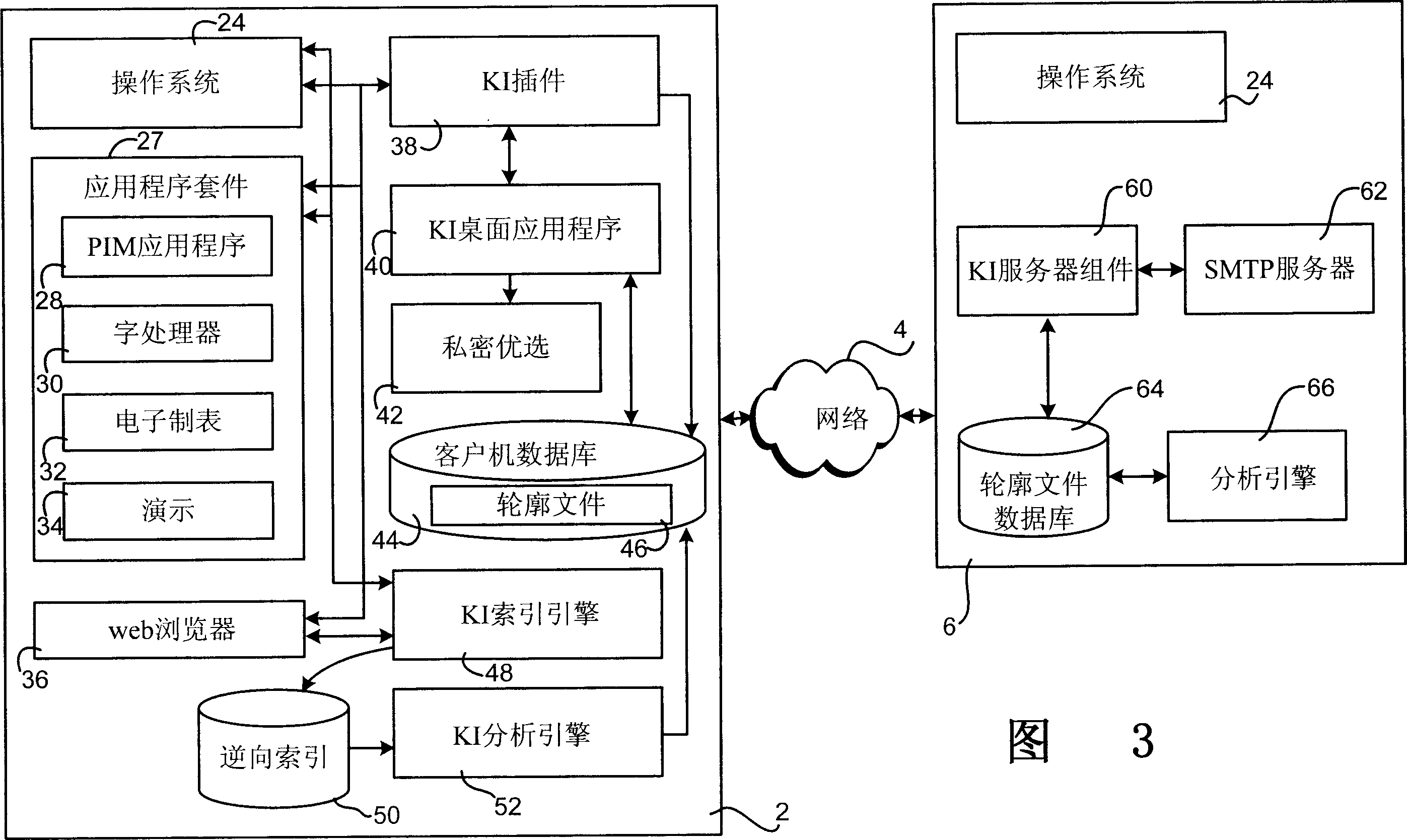
[0021] Referring now to the drawings, wherein like numerals indicate like elements, aspects of the invention will be described. in particular, figure 1 and the accompanying discussion are intended to provide a brief general description of a suitable computing environment in which the invention may be implemented. Although the invention will be described in the general context of program modules executed in connection with an application program running on a personal computer operating system, those skilled in the art will understand that the invention can also be implemented in connection with other types of computer systems and program modules.
[0022] Generally, program modules include routines, programs, components, data structures, and other types of structures that perform particular tasks or implement particular abstract data types. Furthermore, those skilled in the art will appreciate that the present invention may be practiced in other computer system configurations,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com