Secondary authentication method and device
An authentication method and a technology for authenticating equipment, which are applied in the field of communication, can solve problems such as leakage, and achieve the effects of reducing waste, enhancing safety protection, and effectively protecting
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
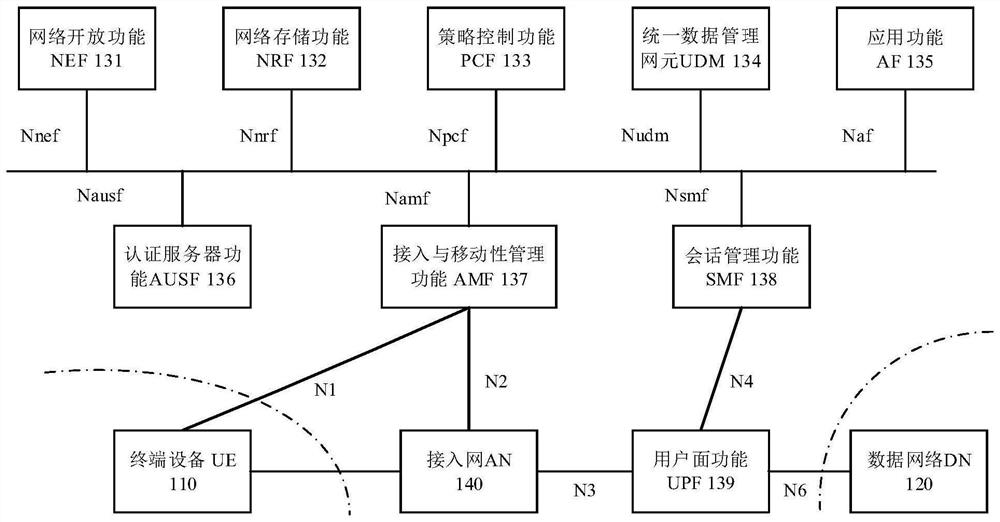
[0074] The technical solution in this application will be described below with reference to the accompanying drawings.
[0075] The technical solution of the embodiment of the present application can be applied to various communication systems, for example: global system of mobile communication (globalsystem of mobile communication, GSM) system, code division multiple access (code division multiple access, CDMA) system, wideband code division multiple access (wideband code division multiple access (WCDMA) system, general packet radio service (general packet radio service, GPRS), long term evolution (long termevolution, LTE) system, LTE frequency division duplex (FDD) system, LTE time division duplex (time division duplex, TDD), universal mobile telecommunications system (universal mobile telecommunications system, UMTS), worldwide interconnection microwave access (worldwide interoperability for microwave access, WiMAX) communication system, fifth generation (5th generation, 5G)...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com