NAT penetration method, device and equipment and storage medium
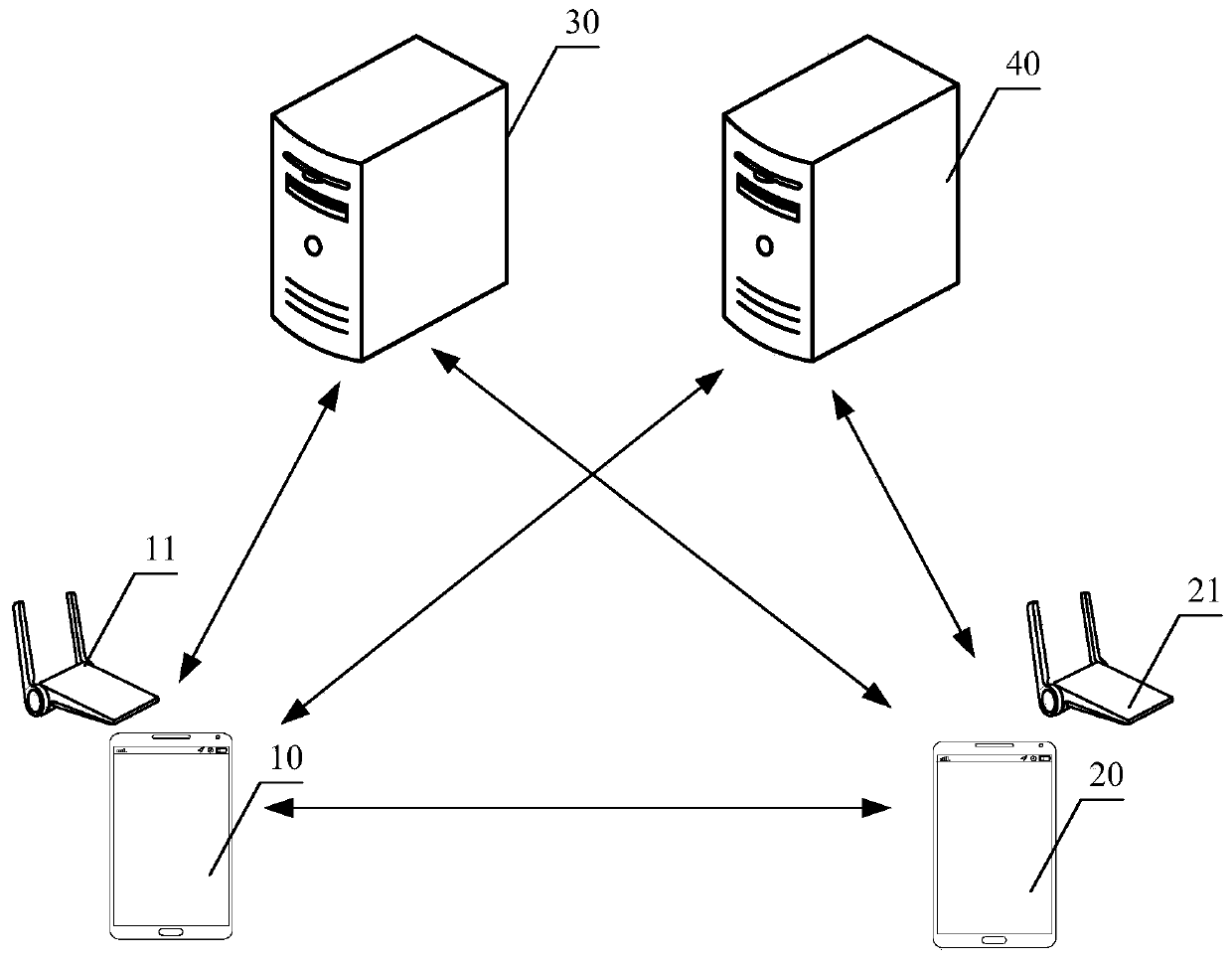
A device and host technology, applied in the Internet field, can solve the problem of low transmission link success rate, and achieve the effect of improving the success rate, reducing the difficulty, and improving the success rate.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
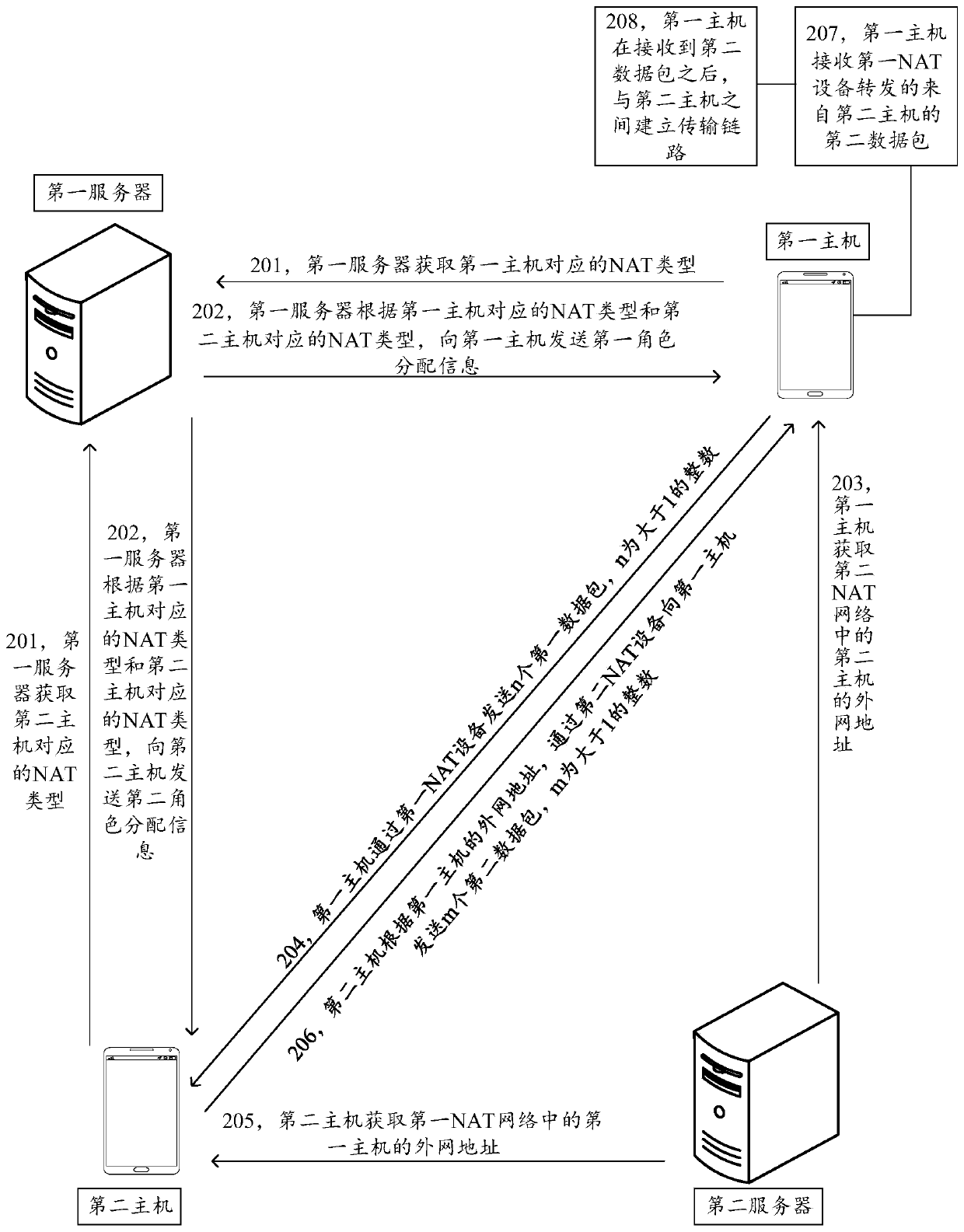
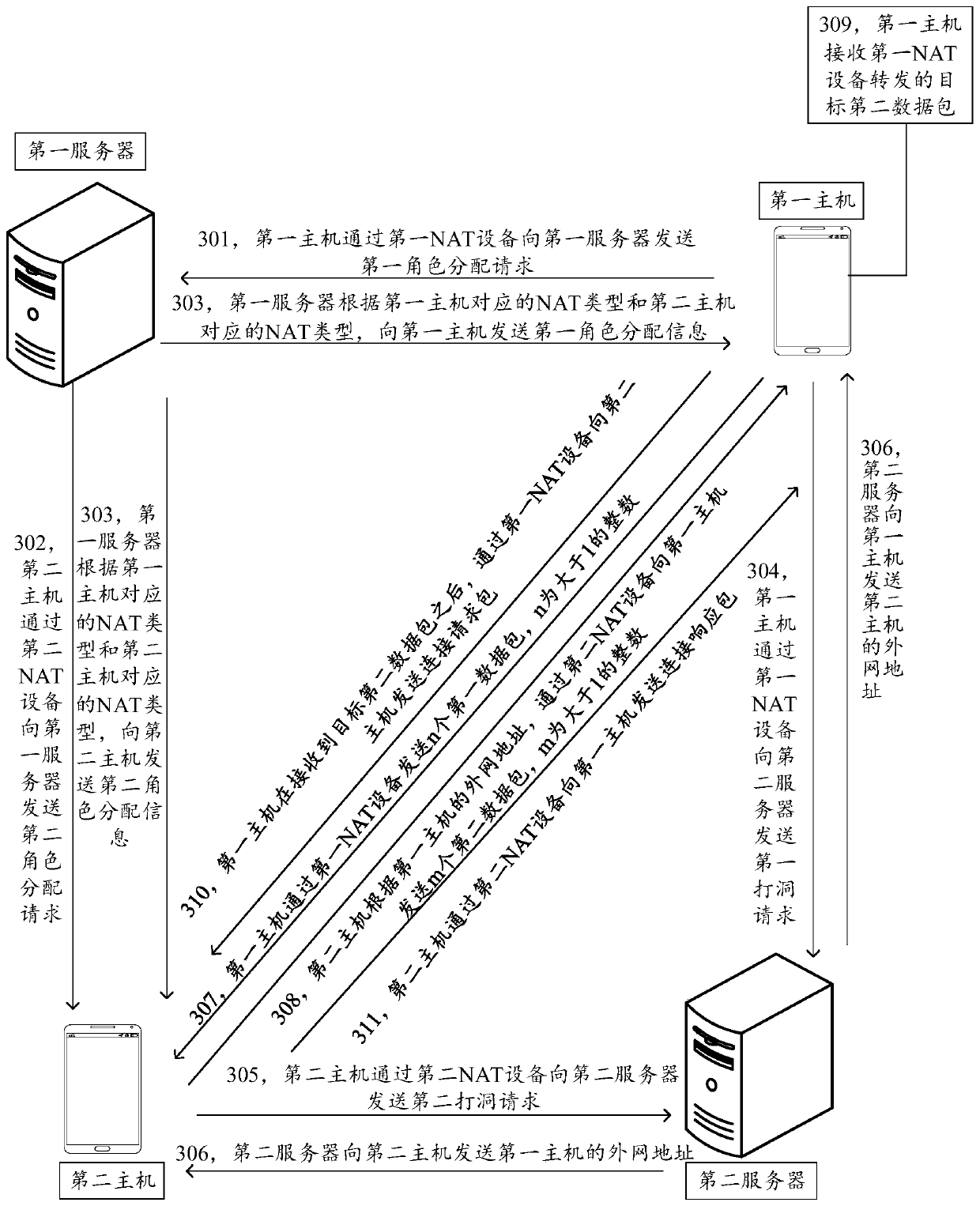
[0058] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
[0059] Before introducing and explaining the embodiment of the present application, the four types of NAT are firstly introduced and explained.
[0060] Full-cone NAT: Connection requests for the same internal network address X (including IP address and port number) will be mapped to the same external network address Y (including IP address and port number), regardless of the destination address of the request. NAT will The request sent by the external address Z (including IP address and port number) to Y is forwarded to X.
[0061] Restricted NAT: Connection requests for the same internal network address X (including IP address and port number) will be mapped to the same external network address Y (including IP address and port ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com