Method and device for implementing management and control strategy of mobile terminal
A technology of mobile terminals and implementation methods, applied in the direction of digital data protection, internal/peripheral computer component protection, instruments, etc., can solve problems such as the inability to realize mobile terminal control, achieve safe and effective control, and ensure complete effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment approach
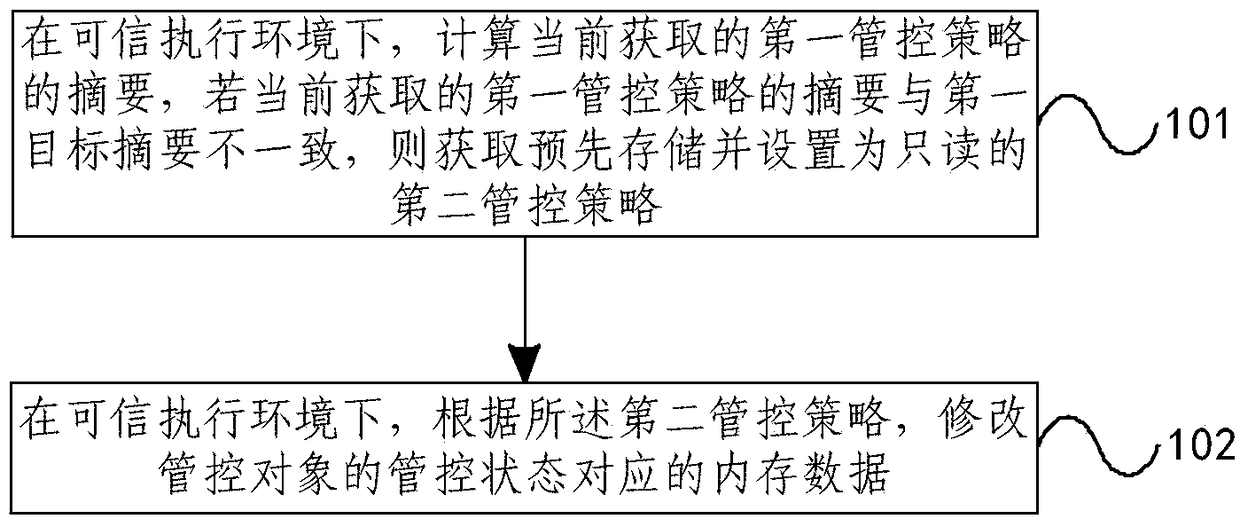
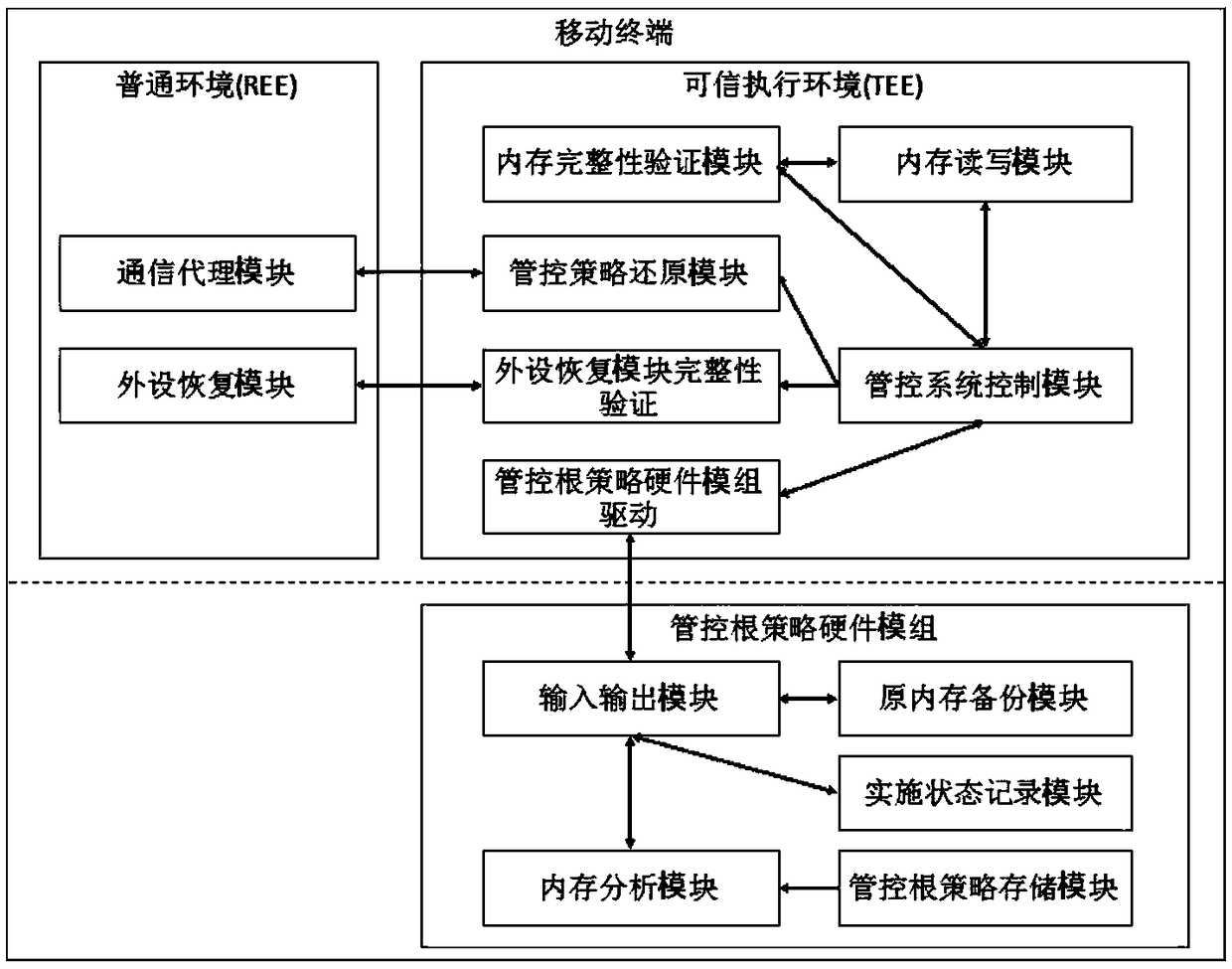
[0023] figure 1 The flow chart of the implementation method of the mobile terminal management and control strategy provided by the embodiment of the present invention, as shown in figure 1 As shown, the embodiment of the present invention provides a method for implementing a mobile terminal management and control strategy, including:
[0024] 101. In a trusted execution environment, calculate the digest of the currently acquired first control policy, and if the currently acquired digest of the first control policy is inconsistent with the first target digest, obtain the pre-stored and read-only second control policy Strategy.
[0025] Before executing 101, it should be noted that the following process is also included:
[0026] In the self-management and control mode, the mobile terminal pre-stores the first management and control strategy, and calculates and stores the first target abstract according to the first management and control strategy. In the interactive manageme...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com