A Secure Transmission Method Based on Symbol Separation and Beamforming in Untrusted Relay Networks
A relay network and secure transmission technology, applied in transmission systems, radio transmission systems, location diversity, etc., can solve problems such as cooperative interference and waste of transmission power
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment approach
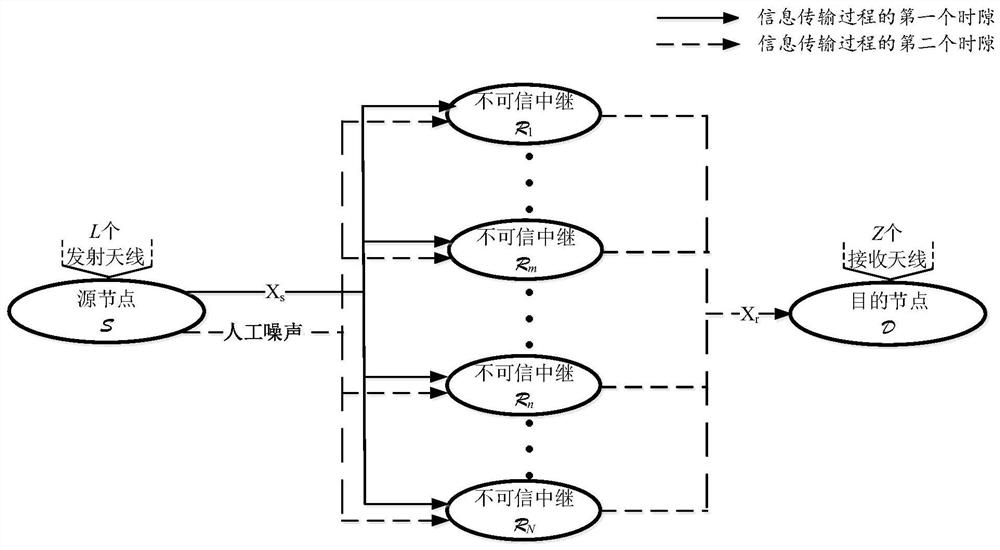
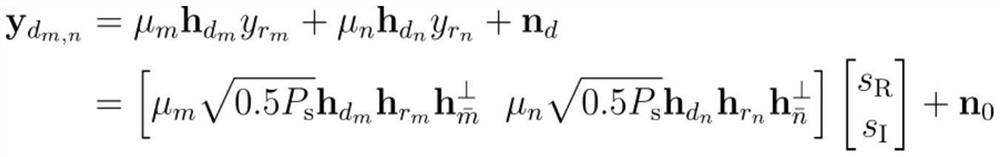
[0052] The specific embodiment of the present invention comprises the following steps:
[0053] first time slot
[0054] In the first time slot of information transmission, operations such as relay selection, precoding design, symbol separation and beamforming, and relay reception are completed respectively. The detailed process is described as follows:
[0055] Define channel matrix means from Channel vector (1≤i≤N) to the i-th relay.
[0056] (1) Relay selection. According to the channel vector Calculate channel gain (||·|| 2 represents the 2-norm of a vector). Select the two relays with the strongest channel gain, namely largest two trunks and Wherein, 1≤i, m, n≤N and m≠n.
[0057](2) Precoding vector and design. for design, it is necessary to send to Ensure that other relays cannot receive in order to guarantee Transmission Security. Similarly, for design, it is necessary to send to Ensure that other relays cannot receive in order ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com