Terminal locking method and device
A locking device and terminal technology, applied in the electronic field, can solve the problems of not being attractive enough, unable to lock the mobile phone, unable to use the SIM card, etc., and achieve the effect of meeting the needs of network locking
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
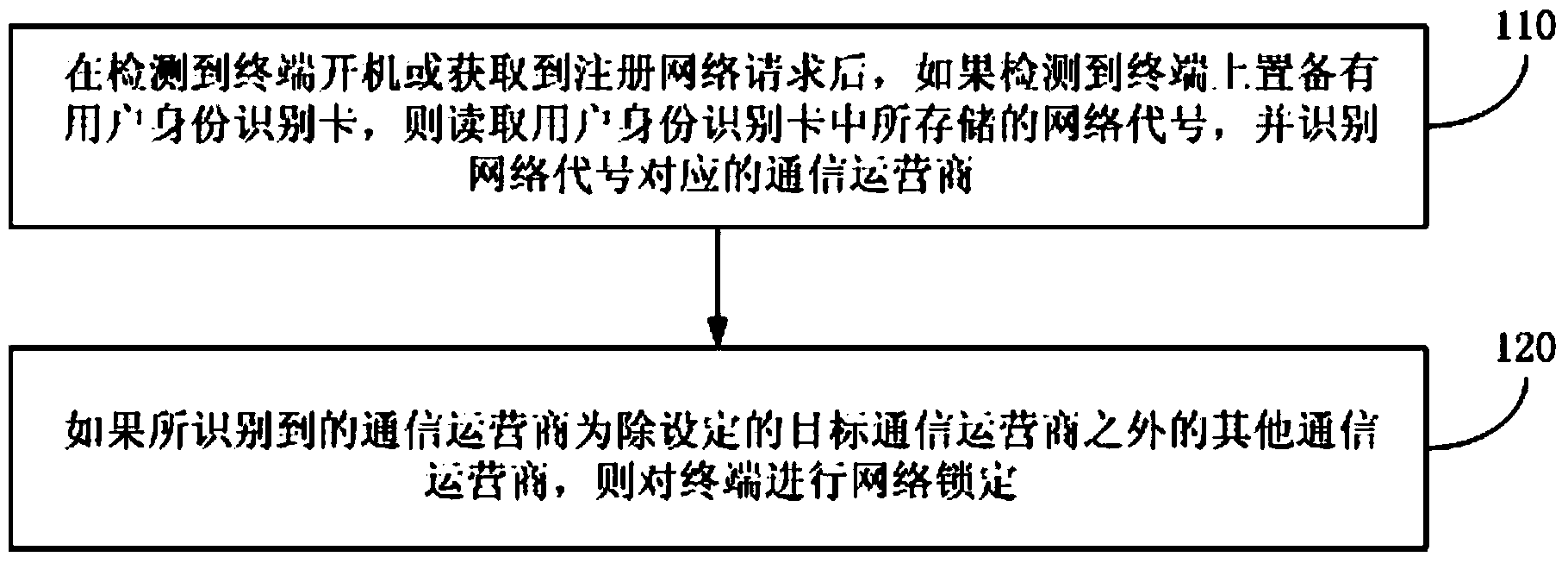
Embodiment 1
[0023] figure 1 It is a schematic flowchart of a terminal locking method provided in Embodiment 1 of the present invention. This embodiment is applicable to the case of network locking of the terminal, especially applicable to the application scenario of network locking of the terminal when a specific communication operator sets the above-mentioned machine-card binding service for the terminal. The terminal locking method provided in this embodiment may be performed by a terminal locking device. The device can be implemented by software and / or hardware, and can be set inside the terminal as a part of the terminal. Wherein, the terminal described in this embodiment is a mobile terminal capable of performing wireless communication based on a SIM card, such as a smart phone. see figure 1 , the terminal locking method provided in this embodiment specifically includes the following operations:
[0024] Operation 110: After detecting that the terminal is turned on or obtaining a...
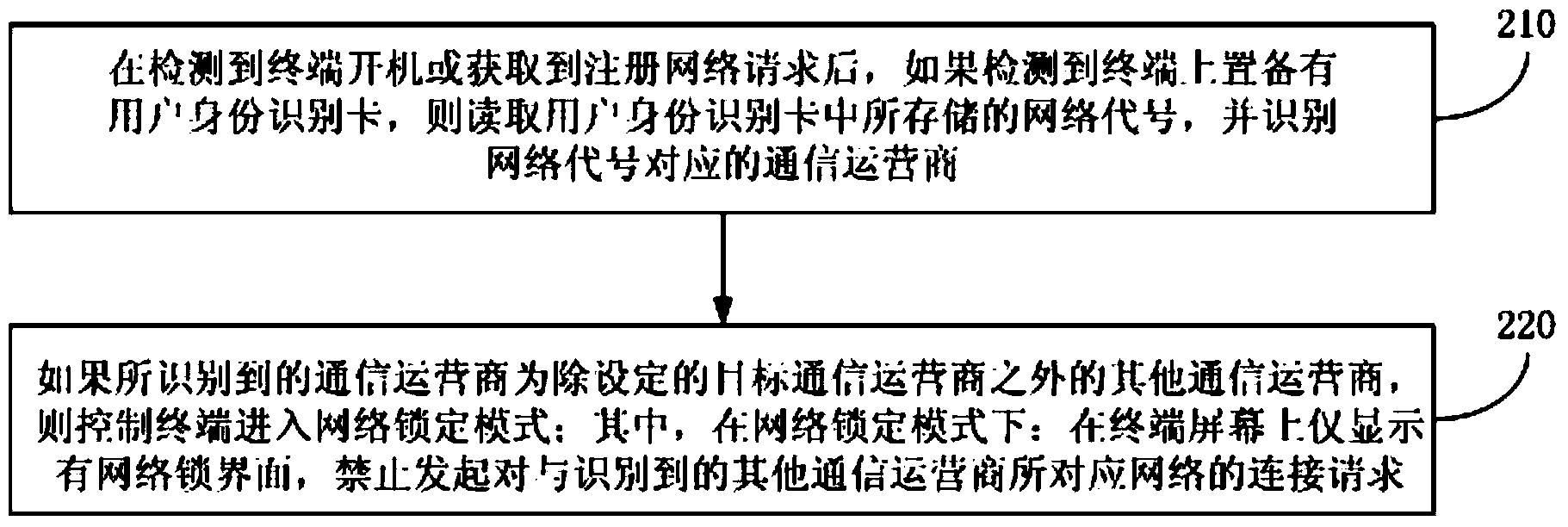
Embodiment 2
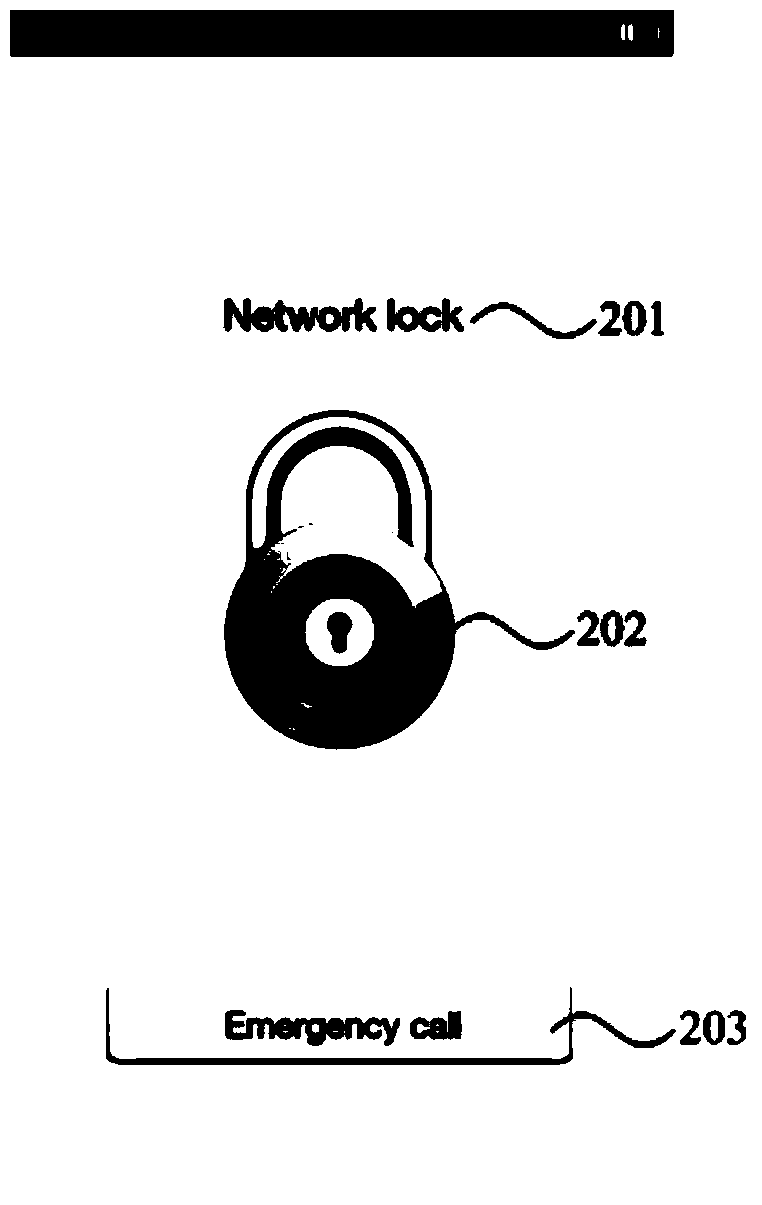
[0034] Figure 2A It is a schematic flowchart of a terminal locking method provided in Embodiment 2 of the present invention. In this embodiment, on the basis of the foregoing embodiments, operation 220 is further optimized. see Figure 2A , the terminal locking method provided in this embodiment specifically includes the following operations:
[0035]Operation 210: After detecting that the terminal is turned on or obtaining a registration network request, if it is detected that the terminal is equipped with a user identification card, read the network code stored in the user identification card, and identify the communication operator corresponding to the network code business;
[0036] Operation 220, if the identified communication operator is a communication operator other than the set target communication operator, control the terminal to enter the network lock mode; wherein, in the network lock mode: only display on the terminal screen There is a network lock interfac...
Embodiment 3
[0044] image 3 It is a schematic flowchart of a terminal locking method provided in Embodiment 3 of the present invention. In this embodiment, on the basis of the second embodiment above, a mechanism for exiting the network lock mode and entering a permanent lock mode is added. see image 3 , the terminal locking method provided in this embodiment specifically includes the following operations:
[0045] Operation 310: After detecting that the terminal is turned on or obtaining a registration network request, if it is detected that the terminal is provided with a user identification card, read the network code stored in the user identification card, and identify the communication operator corresponding to the network code business;
[0046] Operation 320, if the identified communication operator is a communication operator other than the set target communication operator, control the terminal to enter the network lock mode; wherein, in the network lock mode: only display on...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com