Ring signature method for anonymizing information based on multivariate public key cryptography
A multi-variable public key and ring signature technology, applied in the field of information security, can solve problems such as the insecurity of the ring signature system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0127] Anonymous ring signature scheme based on multi-variable public key cryptography TTS(20, 28) system Step 1. Generate system parameters
[0128] 1) Set k=GF(q)=GF(2 8 ) is a finite field characterized by p=2;
[0129] 2) Let m=20 be the number of equations in the multivariate equation system, and n=28 be the number of variables;
[0130] 3) Select H: {0, 1} * →k m is a cryptographically secure anti-collision one-way irreversible hash function,
[0131] The system parameters are (k, q, p, l, m, n, H).
[0132] Step 2. Key Generation
[0133] 1) Suppose there are t users in the ring, set U={u 0 , u 1 ,...,u t-1};
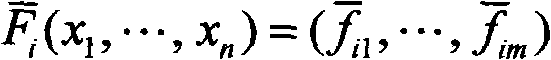
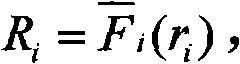
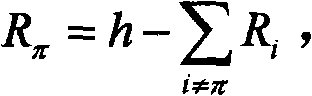
[0134] 2) According to the multivariate public key cryptosystem, each user u i (0≤i≤t-1) choose F from k n to k m The invertible map of F is the central map below
[0135] y i = x i + Σ j = 1 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com