Segment protection method for MPLS-TP network
A network and protection segment technology, applied in the field of protection switching, can solve problems such as protection and inability to provide inter-segment nodes, and achieve the effect of balancing protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
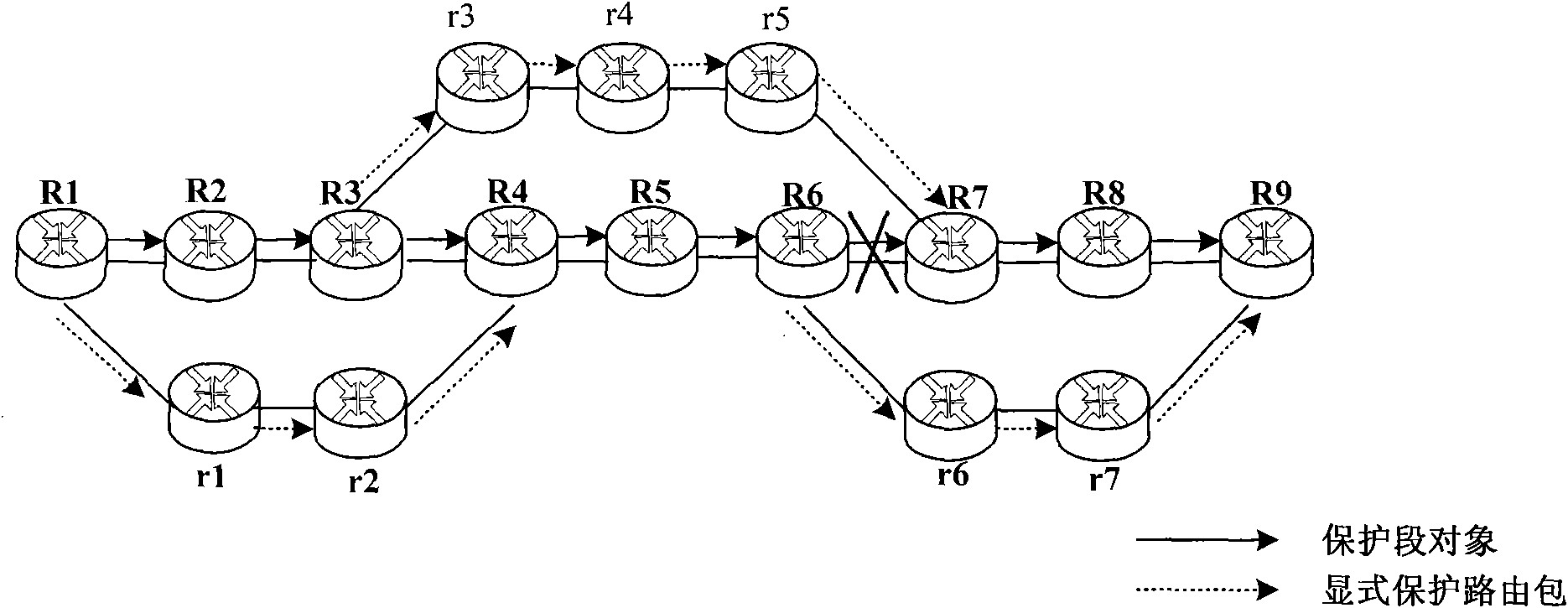
[0022] figure 1 Shown is an LSP working path machine protection segment path in the MPLS-TP network, where the working LSP is R1→R2→R3→R4→R5→R6→R7→R8→R9. Here, the overlapping segment protection mechanism is taken as an example. The LSP is divided into three working segments (WS), namely: WS1(R1→R2→R3→R4), WS2(R3→R4→R5→R6→R7), WS3(R6→R7→R8→R9) . The corresponding protection sections (PS) are: PS1 (R1→r1→r2→R4), PS2 (R3→r3→r4→r5→R7), PS3 (R6→r6→r7→R9).
[0023] The transmission path of the Path message including the PSO is the working LSP (R1→R2→R3→R4→R5→R6→R7→R8→R9).
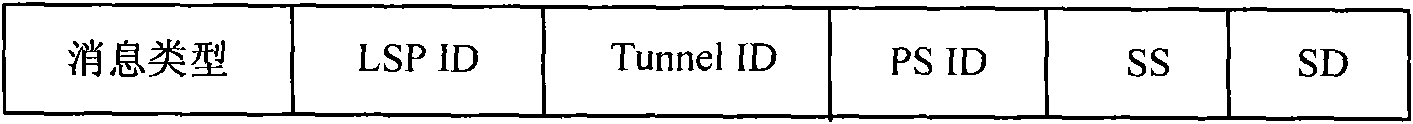
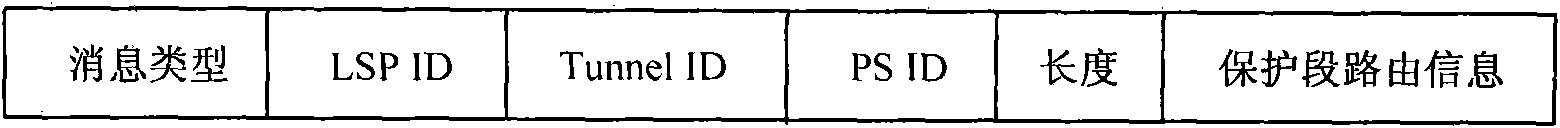
[0024] figure 2 Shown is the message format of the protection segment object (PSO), and its structure is as follows:
[0025] ●Message type: 8bit, indicating the type of the control object;
[0026] ●LSP ID: 16bit, indicating the LSP number of the working path protected by the pro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com