Safety verification method and device based on mouse track and computer equipment
A mouse trajectory and security verification technology, applied in the computer field, can solve problems affecting the normal user experience, etc., and achieve the effects of high speed, security and high efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] Embodiments of the present application are described in detail below, examples of which are shown in the drawings, wherein the same or similar reference numerals denote the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary, and are intended to explain the present application, and should not be construed as limiting the present application.
[0028] The mouse track-based security verification method, device, computer equipment, and storage medium of the embodiments of the present application are described below with reference to the accompanying drawings.
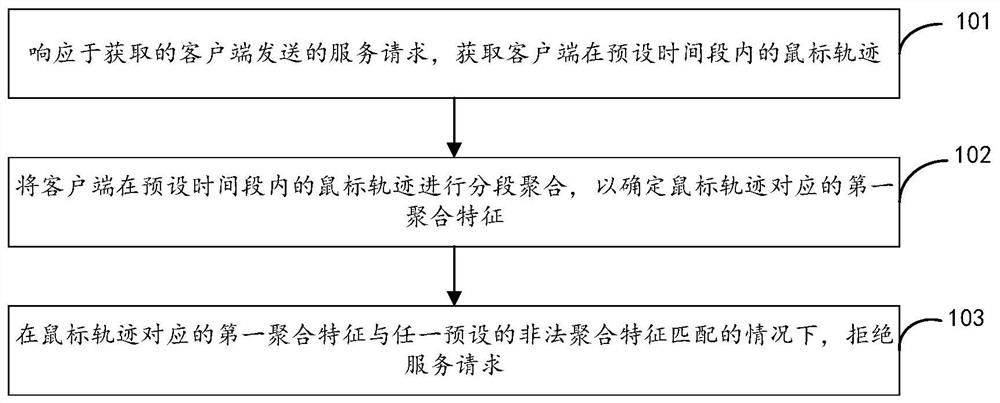
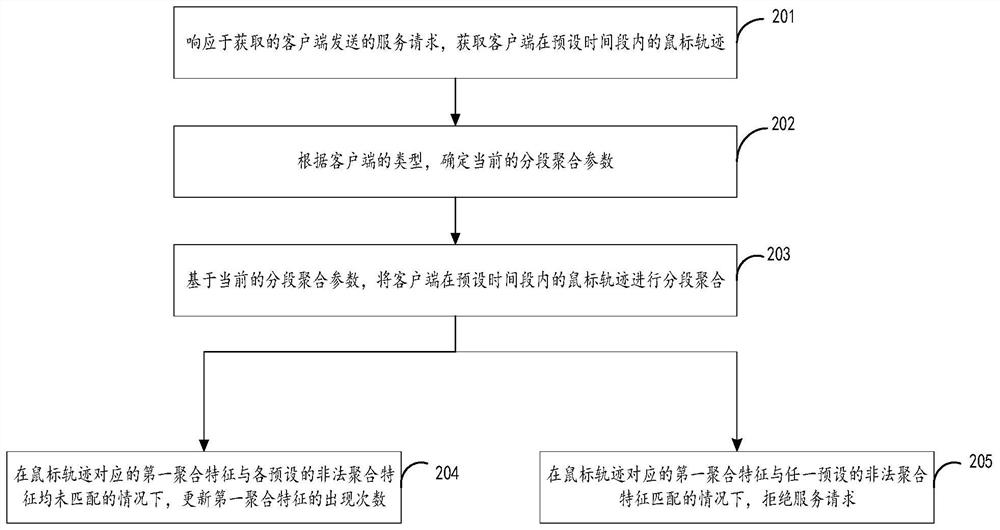
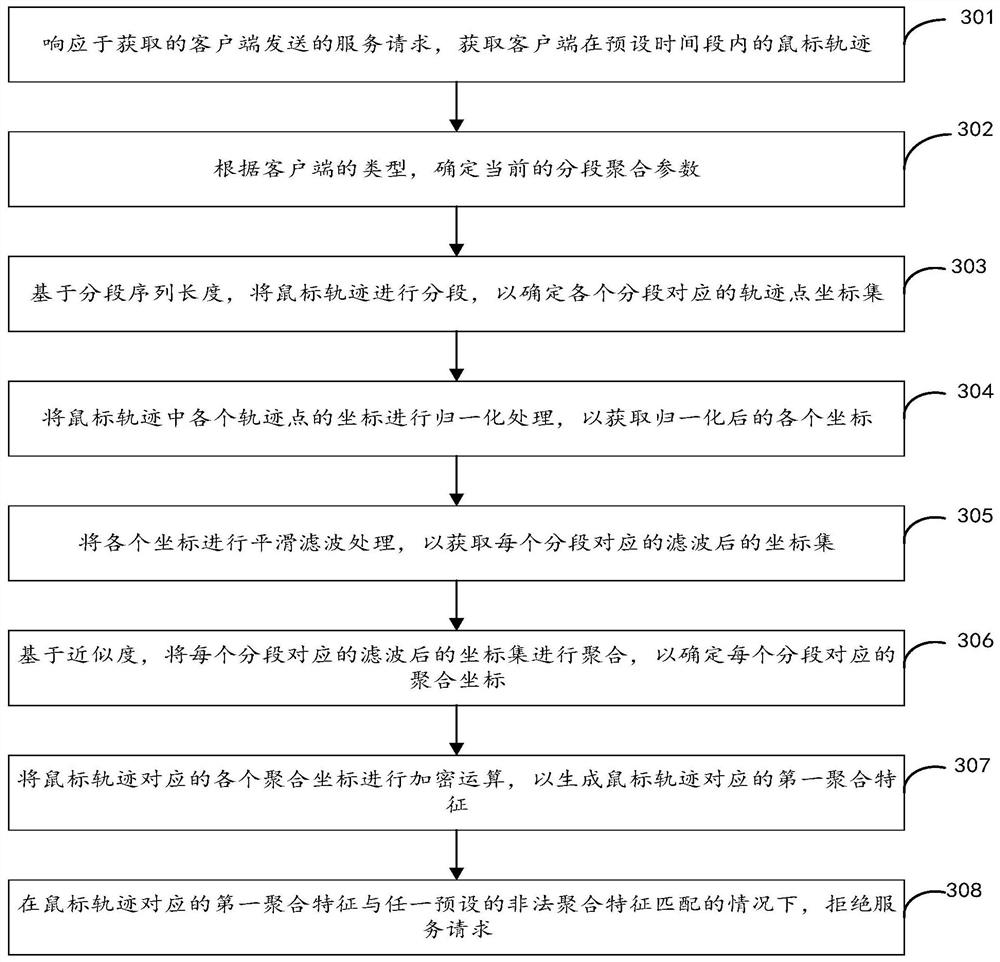
[0029] figure 1 It is a schematic flowchart of the mouse track-based security verification method provided by the embodiment of the present application.
[0030] In the embodiment of the present application, the mouse track-based security check method is configured in a mouse track-based security check device...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com