Alarm correlation analysis method based on attack scene construction
A technology of correlation analysis and attack scenarios, which is applied in the field of alarm correlation analysis based on attack scenarios, and can solve the problems of difficulty in finding attack scenarios, failure to achieve better correlation efficiency, and single role.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] Embodiments of the present invention are described in detail below, examples of which are shown in the drawings, wherein the same or similar reference numerals designate the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary and are intended to explain the present invention and should not be construed as limiting the present invention.
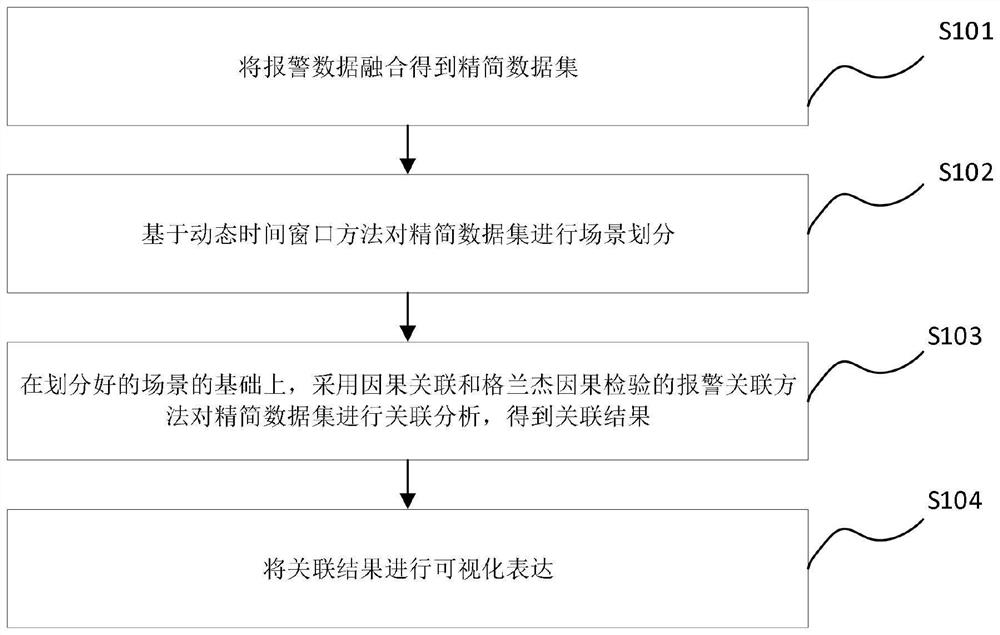
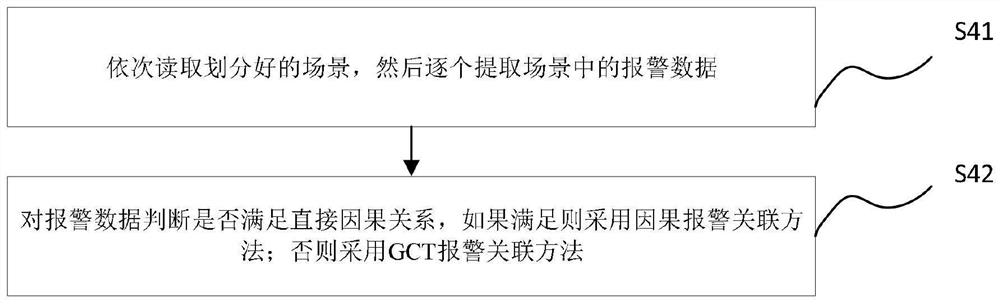
[0041] see Figure 1 to Figure 5 , the present invention provides an alarm correlation analysis method based on attack scenarios, including:
[0042] S1 fuses the alarm data to obtain a simplified data set;
[0043] The experiment uses the honeypot data set and the laboratory collects the alarm data as the original data set by building a real intrusion detection environment. Firstly, the raw alarm data is preprocessed.
[0044] Data processing flow:
[0045] Step 1: First, the alarm data attributes need to be extracted, and t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com