Database dynamic desensitization method and system based on TCP proxy
A database and desensitization technology, which is applied in the field of information security, can solve the problems of low possibility of reuse, few applicable scenarios, and high cost of scenario switching, and achieve the effects of high availability, easy implementation, and linear scalability of performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
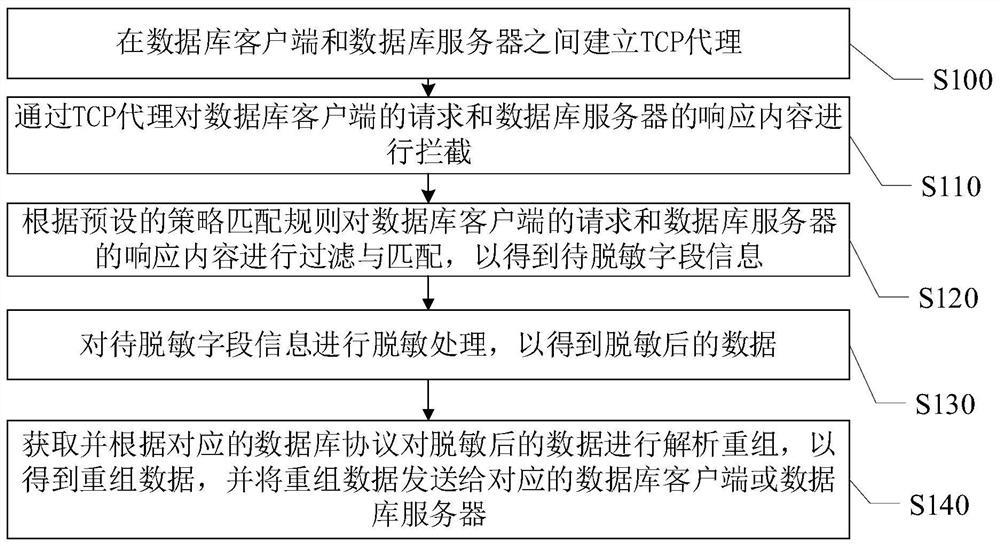
[0030] see figure 1 , figure 1 A schematic diagram of steps of a TCP proxy-based database dynamic desensitization method provided by the embodiment of the present invention is as follows:
[0031] Step S100, establishing a TCP proxy between the database client and the database server;
[0032]Step S110, intercepting the request of the database client and the response content of the database server through the TCP proxy;
[0033] Step S120, filtering and matching the request of the database client and the response content of the database server according to a preset policy matching rule to obtain field information to be desensitized;
[0034] Step S130, performing desensitization processing on the field information to be desensitized to obtain desensitized data;
[0035] Step S140: Acquire and analyze and reorganize the desensitized data according to the corresponding database protocol to obtain reorganized data, and send the reorganized data to the corresponding database cl...
Embodiment 3
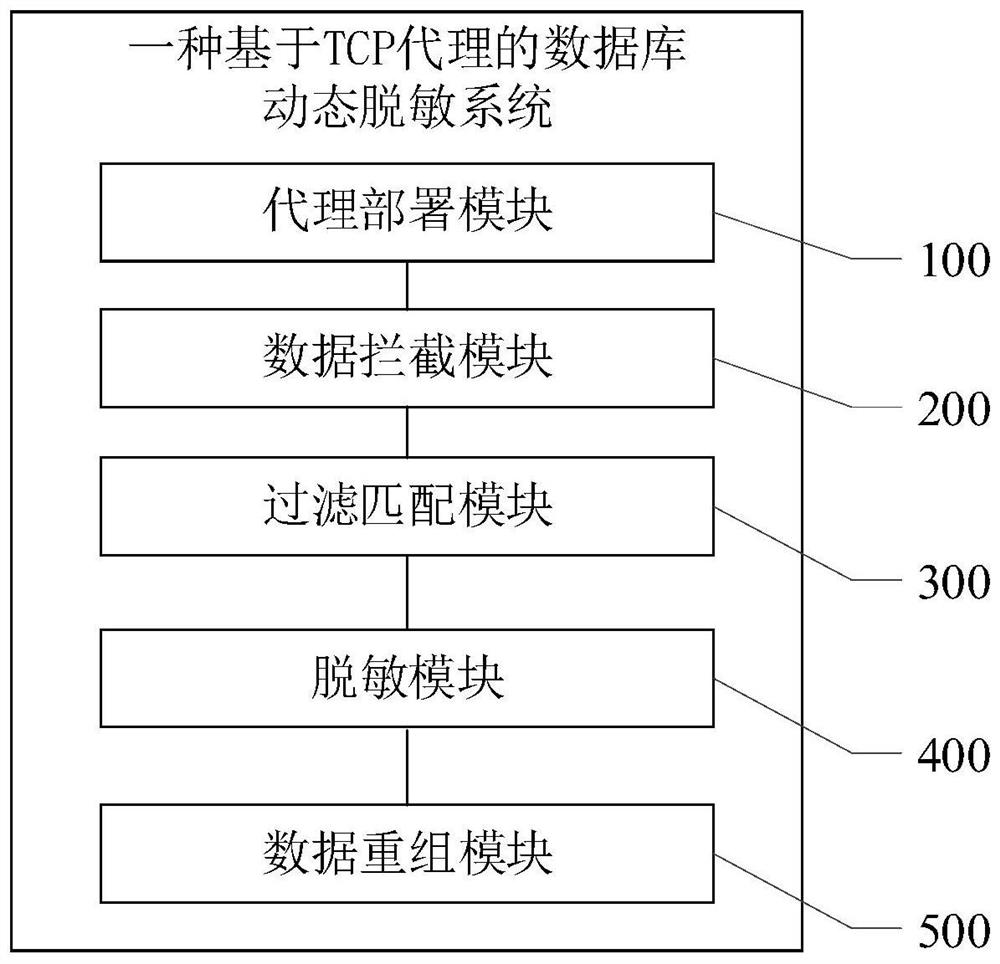
[0045] see figure 2 , figure 2 A schematic diagram of a TCP proxy-based database dynamic desensitization system module provided by the embodiment of the present invention is as follows:
[0046] The proxy deployment module 100 is used to establish a TCP proxy between the database client and the database server;
[0047] The data interception module 200 is used for intercepting the request of the database client and the response content of the database server through the TCP proxy;
[0048] The filtering and matching module 300 is used for filtering and matching the request of the database client and the response content of the database server according to a preset policy matching rule, so as to obtain the field information to be desensitized;
[0049] The desensitization module 400 is used to desensitize the field information to be desensitized to obtain desensitized data;
[0050] The data reorganization module 500 is used to obtain and analyze and reorganize the desensi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com