Early warning method and device for arp entry spoofing attack on local area network
An ARP table entry and spoofing attack technology, applied in the field of network communication, can solve problems such as user network connection failure, and achieve the effect of preventing spoofing attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
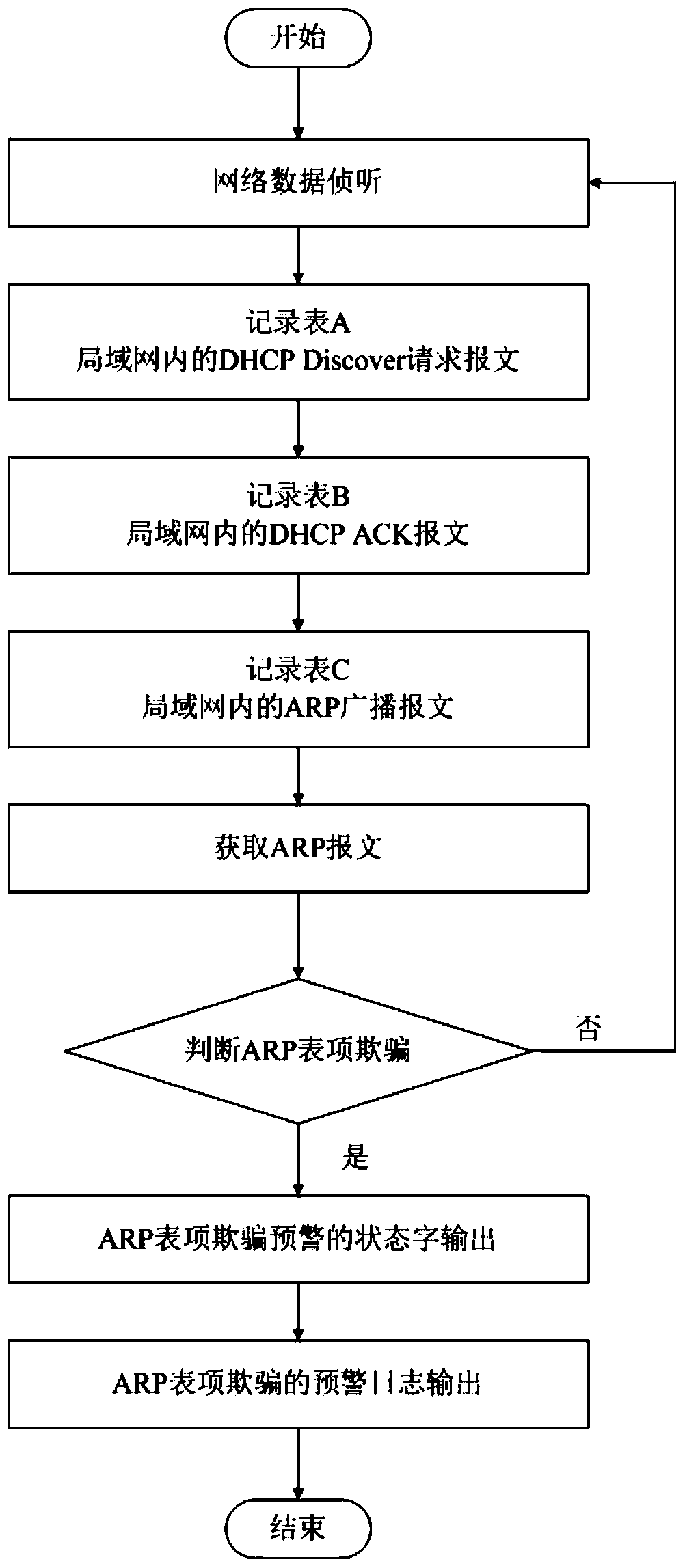
[0015] Embodiment 1: a kind of early warning method for the ARP entry spoofing attack of local area network, comprises the following steps:
[0016] S1. Network data interception;
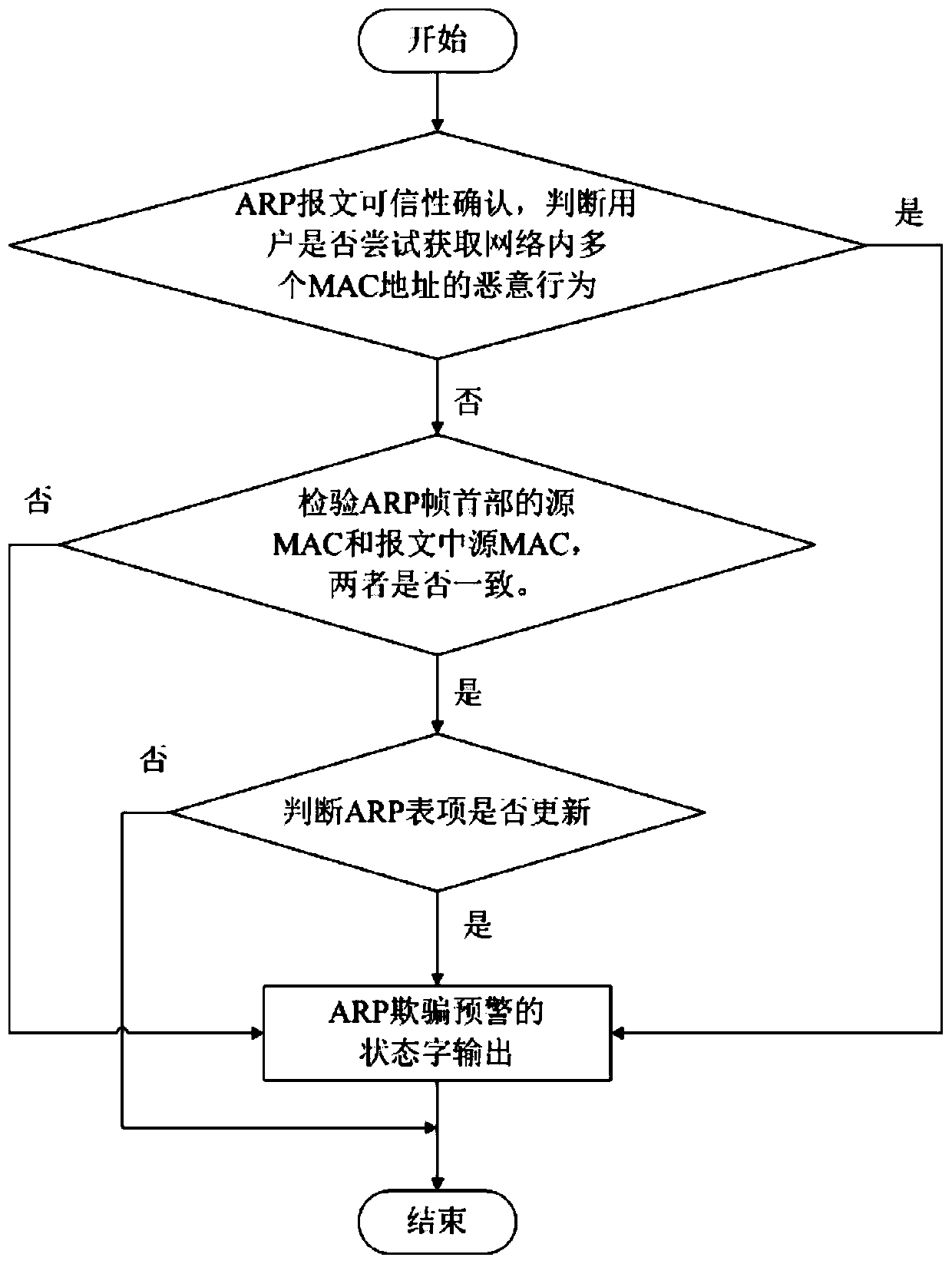
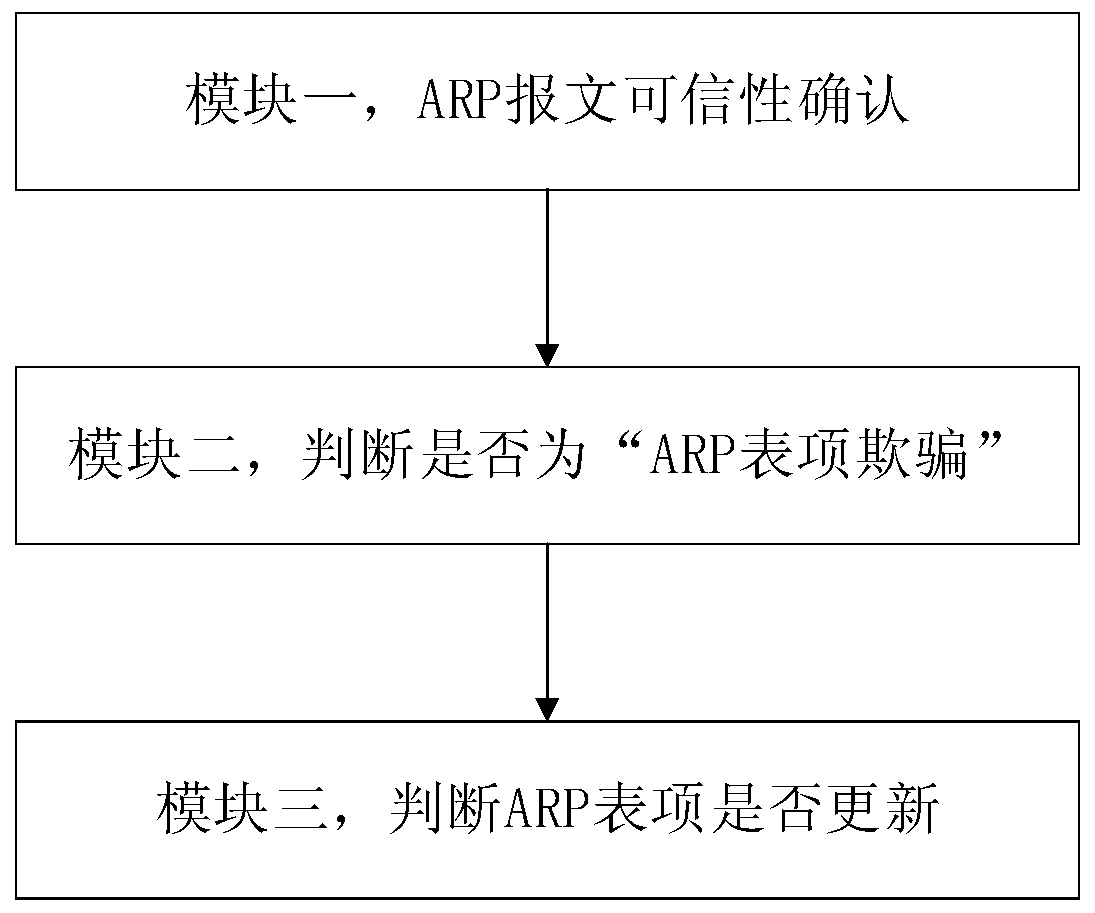
[0017] S2. ARP message authenticity confirmation;
[0018] S2.1. When the ARP message is untrustworthy, perform an early warning judgment on ARP entry spoofing;
[0019] S2.2. When the ARP message is authentic, analyze the ARP message entry to determine the ARP entry spoofing.
[0020] As a kind of embodiment, in its described step S1, network data interception is: obtain the DHCPDiscover request message in the network, record in table A; Obtain the DHCP ACK message in the network, record in table B; Obtain ARP broadcast packets in the network are recorded in Table C.
[0021] As an embodiment, the specific steps of its step S2 are: analyze the IP address of the ARP request packet sent by the user, judge whether it appears in Table A and Table C, and judge whether it is stored in the static IP a...
Embodiment 2
[0040] Embodiment 2: As a supplement to the technical solution of Embodiment 1 or as a separate embodiment, this embodiment provides an early warning method for ARP entry spoofing attacks on a local area network. First listen through network data frames. Obtain the DHCPDiscover request message in the network and record it in table A; at the same time obtain the DHCPACK message and record it in table B; at the same time obtain the ARP broadcast message in the network and record it in table C. Then compare the data in the above record table to confirm the credibility of the ARP message, analyze the ARP message entry, and analyze whether the source MAC in the ARP frame header and the source MAC in the message are consistent. Whether to update the ARP entry, whether it meets the characteristics of ARP spoofing. If it meets the characteristics of ARP spoofing, then output the status word of ARP spoofing attack alarm. Then output the log of ARP spoofing attack alarm. The program ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com