An encrypted interaction method between a sim card and a dedicated public telephone terminal and the dedicated public telephone terminal
An interactive method and public telephone technology, applied in the field of communication, can solve the problem of reducing the profit and income of mobile operators, and achieve the effect of preventing possibility and information leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
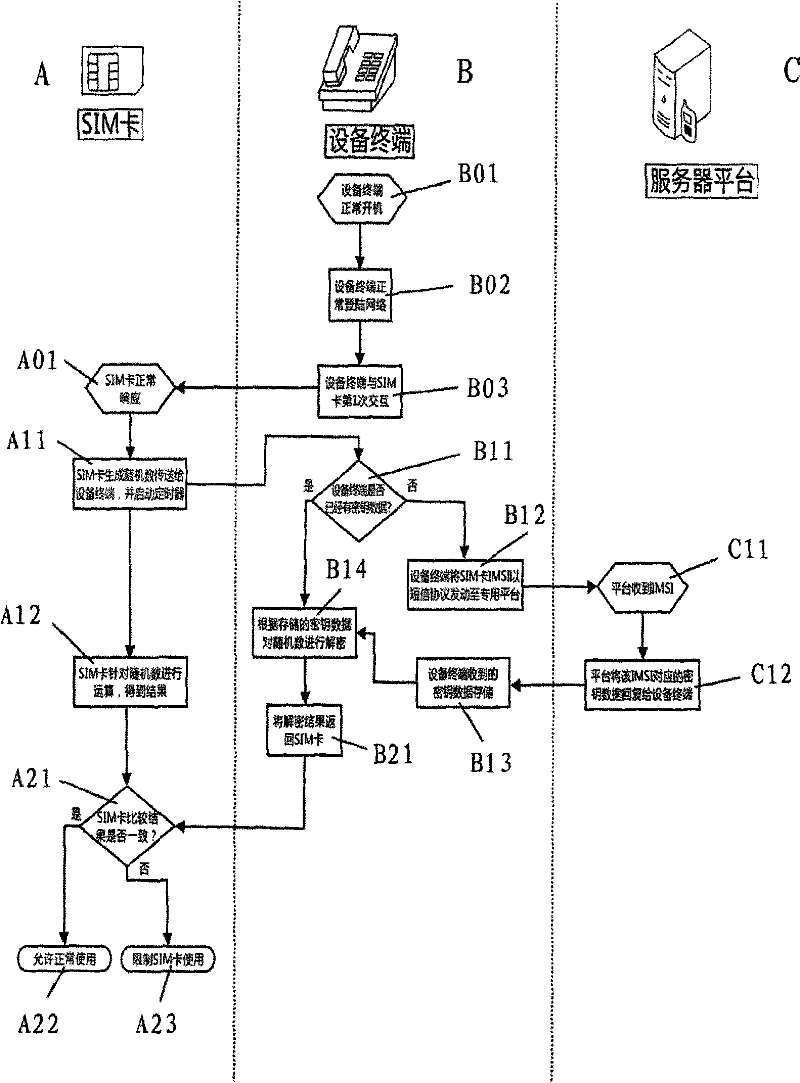
[0047] The present invention will be further described in conjunction with the accompanying drawings and specific embodiments.
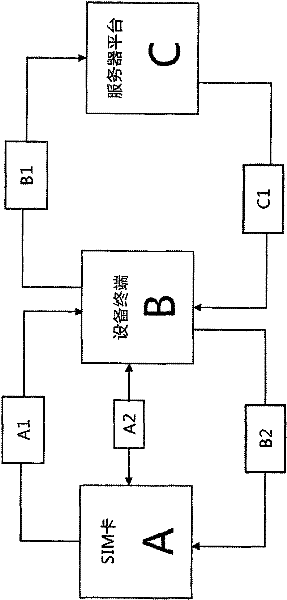
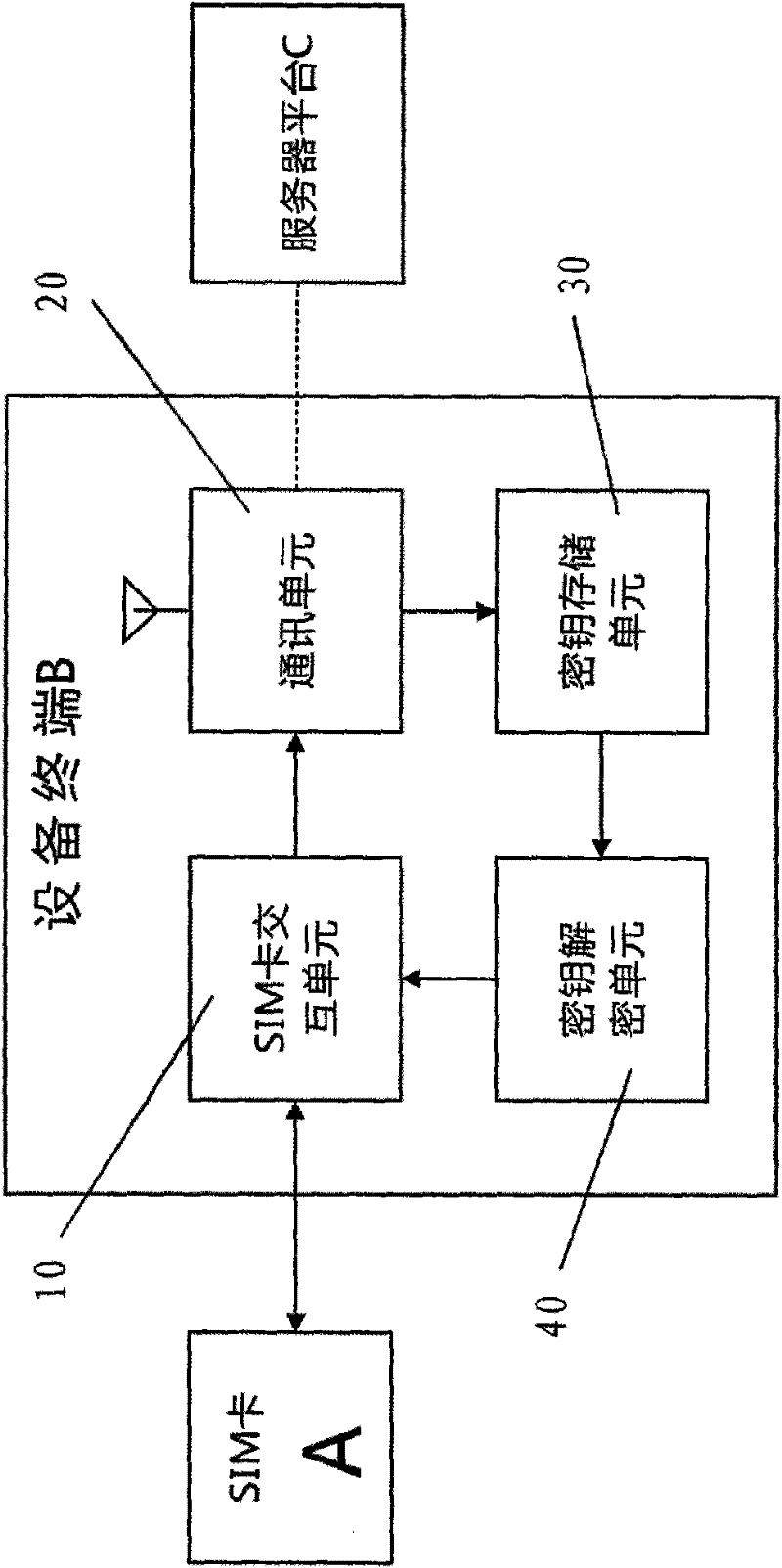
[0048] refer to figure 1 As shown, the embodiment of the present invention includes the following steps:
[0049] Step A1: SIM card A transmits a random number to device terminal B;
[0050] Step B1: The device terminal B responds and sends the IMSI of the SIM card A to the server platform C;
[0051] Step C1: server platform C responds and sends a key to device terminal B;
[0052] Step B2: Device terminal B responds and returns the key calculation result to SIM card A;
[0053] Step A2: SIM card A responds and allows or restricts usage after comparing the results.
[0054] The principle of encrypted interaction between SIM card A and device terminal B is: public phone SIM card A transmits a 20-byte random number (RND) to phone device terminal B through the GetInput command (GSM11.14 standard command). Mobile phone device terminal B uses the fi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com