Method for monitoring network border security
A network boundary and security monitoring technology, applied in the direction of data exchange network, digital transmission system, electrical components, etc., can solve the problems of inability to process and locate security events, single-handedly understand the monitoring information of users, application systems or traffic, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] In order to make the technical means, creative features, goals and effects achieved by the present invention easy to understand, the present invention will be further described below in conjunction with specific illustrations.
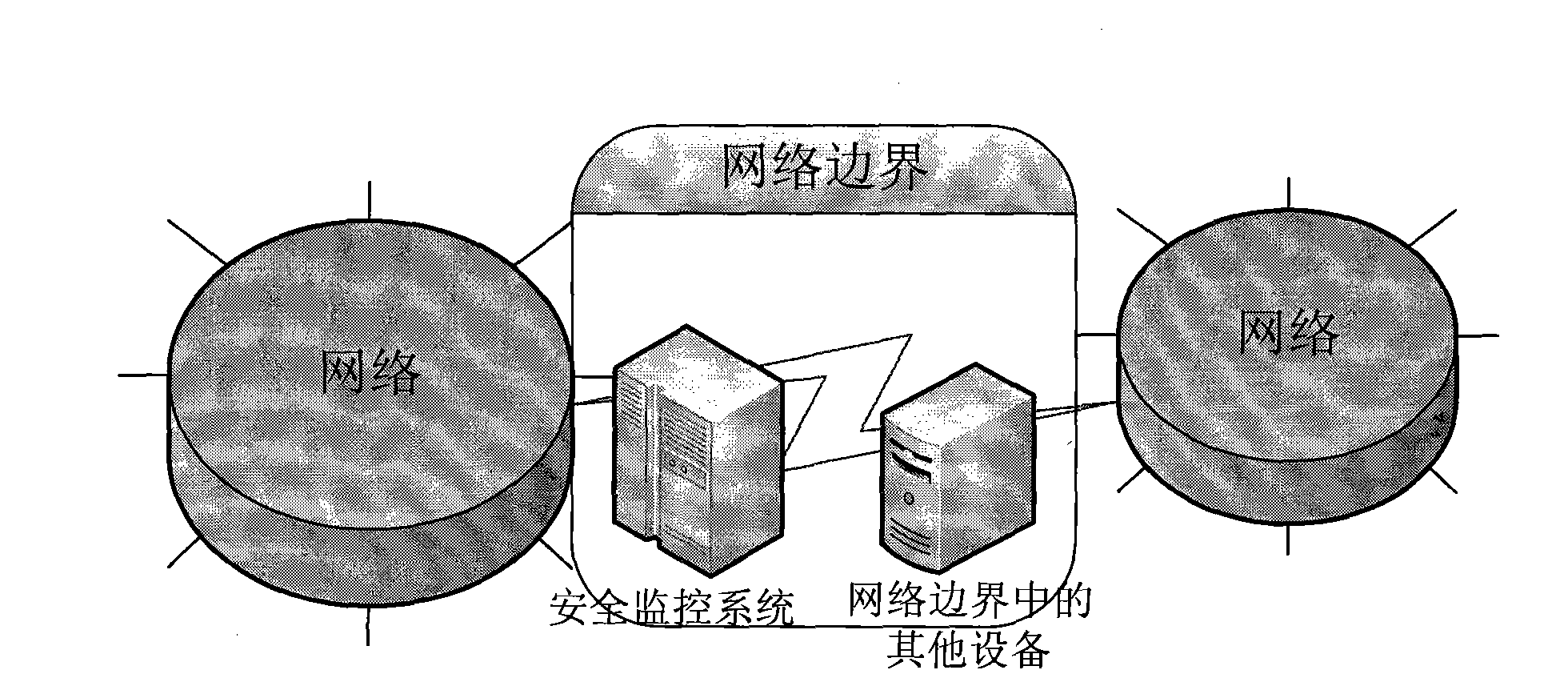
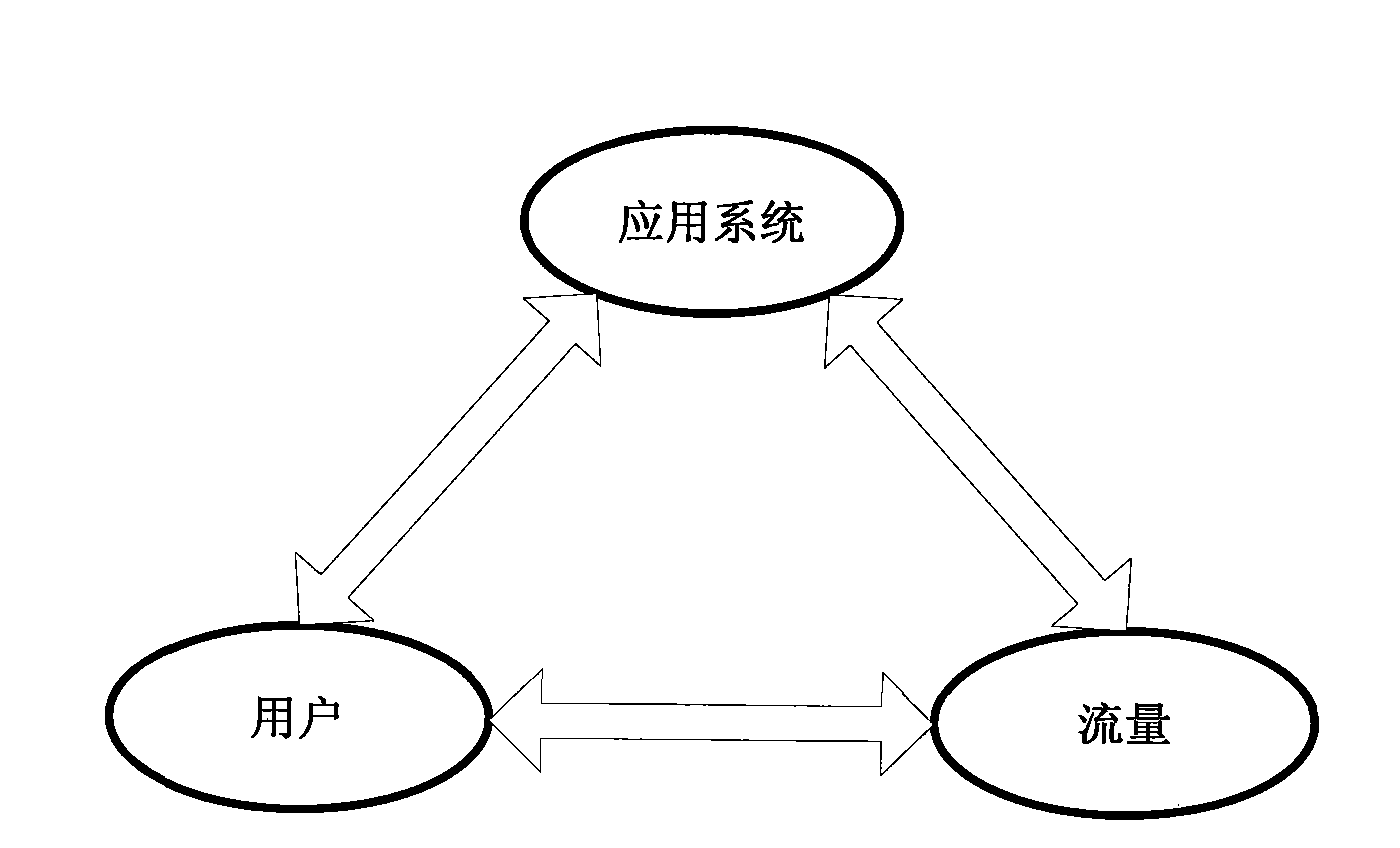
[0021] Such as figure 1 As shown, a network boundary security monitoring method, a security monitoring system is set in the network boundary between networks, and the security monitoring system includes corresponding monitoring modules for monitoring the flow, users and application systems of the network boundary, and will The monitoring module monitors the network border traffic, user and application system information for correlation analysis, and can obtain all monitoring information of network border traffic, user and application system information through one of the traffic, user or application system information.
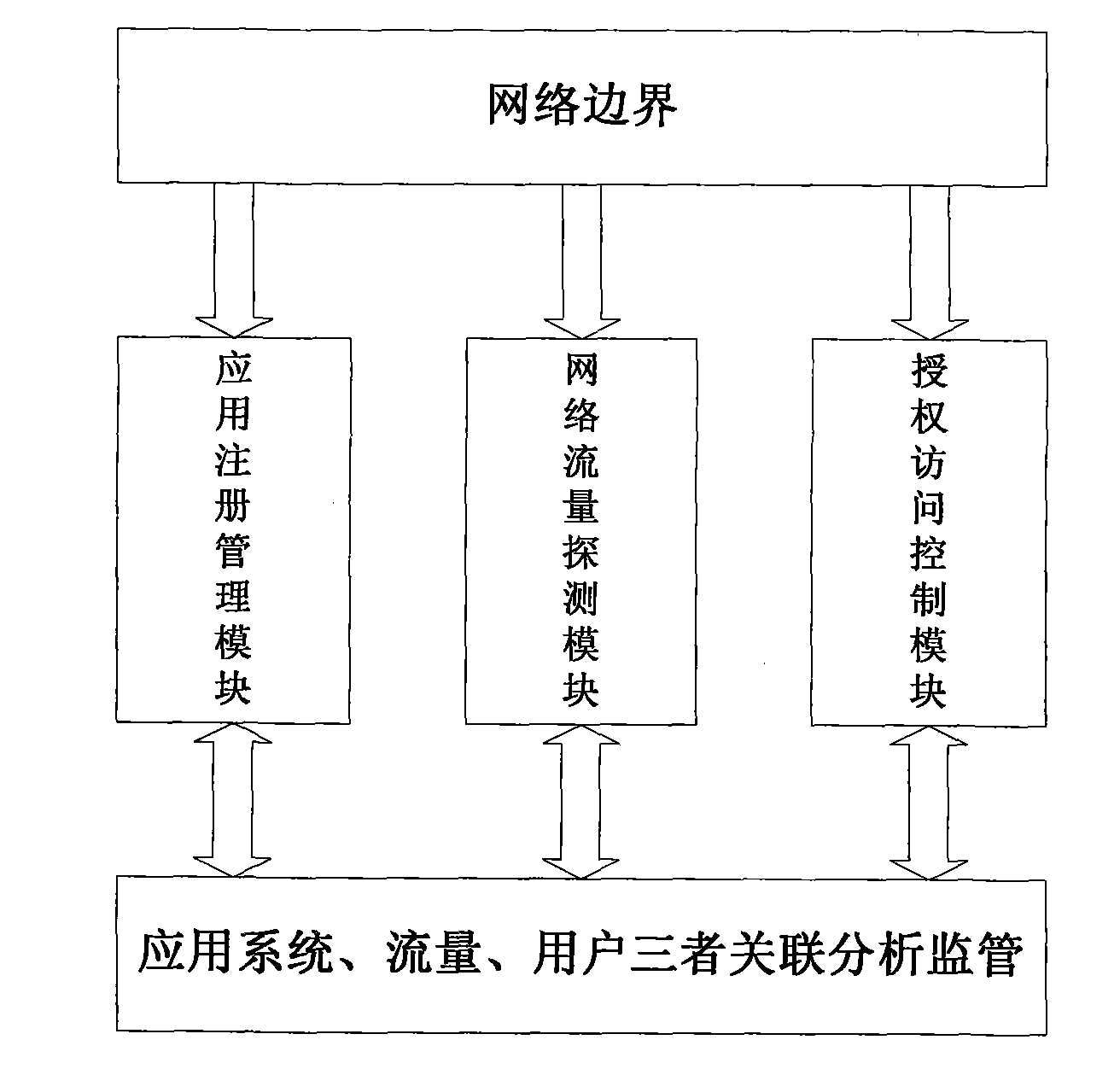
[0022] Such as figure 2 As shown, in one embodiment of the present invention, the security monitoring system includes an app...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com