The random number encryption method used to generate access requests initiated by the service provider
A technology of access request and encryption method, applied in the direction of transmission system, electrical components, etc., can solve the problems of increasing the size of third-party APP, long access period, data leakage, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
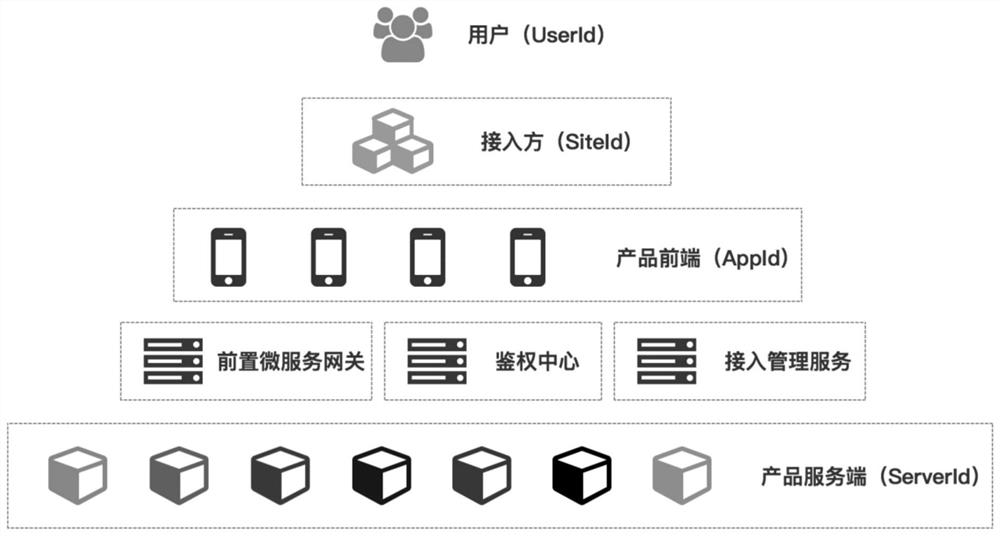
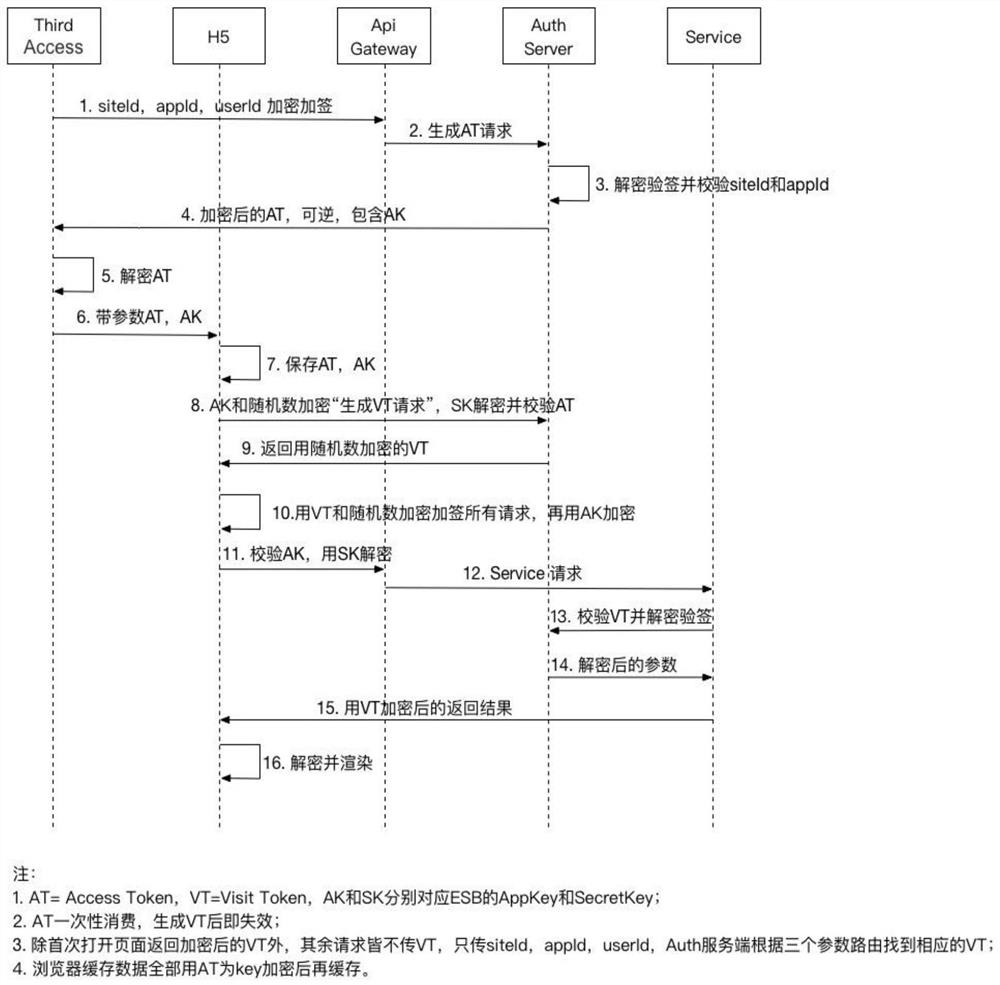
[0010] Such as Figure 1 to Figure 2As shown, the third-party security access method in the form of H5 application of the service provider includes the third-party backend, the H5 end of the service provider, the gateway server of the service provider, the authentication end of the service provider, and the backend of the service provider. It includes the following steps: A. The user of the third-party client clicks on an entry to request to enter the service application provided by the service provider, and notifies the third-party backend of the message; B. The third-party backend sends a message to the The service provider initiates a request to generate an access key AT (Access Token, referred to as AT), and the service provider generates the access key AT and sends it back to the third-party backend through the service provider gateway server; C, the third-party backend After the end receives the encrypted AT, it decrypts the AT, and reverses the AT to obtain AK (AppKey, ...
Embodiment 2
[0013] The service provider initiates the random number encryption system for generating access requests, including the service provider H5 end, the service provider gateway server end, and the service provider authentication end, among which:
[0014] The service provider H5 terminal is used to initiate a request to the service provider to generate an access key VT through the service provider gateway server. The requested parameters include the access key AT, and the access key AT uses a random number as a key to encrypt, also use
[0015] It is used to receive the access key VT generated by the service provider’s authentication terminal through the gateway server of the service provider, and is also used to decrypt the VT through random numbers, open and render the H5 product page, and carry out various external services of the H5 product; The authentication terminal of the service provider is used to decrypt the request for generating the access key VT after receiving the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com