An authentication method, device and system for preventing a lock from being copied, and an electronic key
An electronic key and authentication method technology, applied in the field of industrial security, can solve problems such as the inability to prevent locks from being copied, and achieve the effect of eliminating integration into the lock management system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
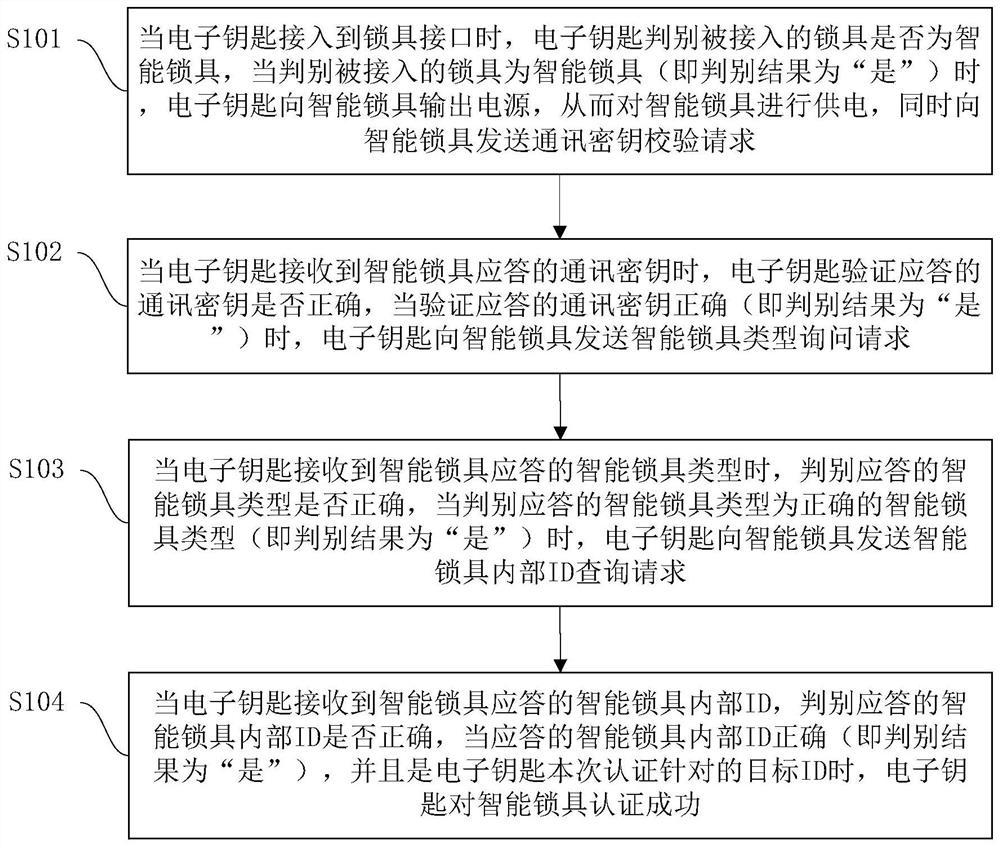
[0046] An authentication method to prevent the lock from being copied proposed by the embodiment of the present invention, such as figure 1 shown, including:
[0047] Step S101: When the electronic key is connected to the lock interface, the electronic key judges whether the connected lock is a smart lock, and when it is judged that the connected lock is a smart lock (that is, the judgment result is "Yes"), the electronic key sends The smart lock outputs power to supply power to the smart lock, and at the same time sends a communication key verification request to the smart lock;
[0048] The operation of judging whether the connected lock is an intelligent lock can be called an intelligent lock type identification operation.
[0049] In one embodiment, non-contact RFID identification and / or magnetic induction sensor technology is used to determine whether the locked lock is a smart lock. In some embodiments, the following methods can be used to determine whether the connected...
Embodiment 2
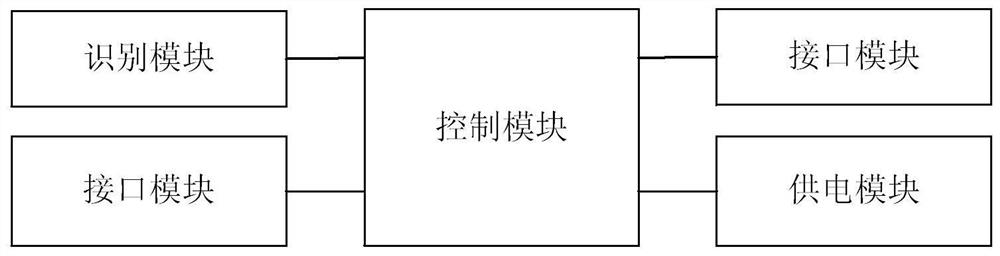
[0071] An electronic key used to prevent locks from being copied proposed by an embodiment of the present invention, such as figure 2 As shown, it includes: a control module, a power supply module, an interface module, an identification module and a prompt module. The power supply module, interface module, identification module and prompt module are all connected with the control module, and the control module controls the operation of the power supply module, interface module, identification module and prompt module.
[0072] The power supply module is used for supplying power to the lock according to the instruction of the control module. The power supply module can supply power to the lock by means of contact power supply or non-contact power supply.
[0073] The interface module is used to send sensing signals or requests to the lock according to the instructions of the control module, and obtain corresponding feedback information from the lock; the obtained feedback inf...
Embodiment 3
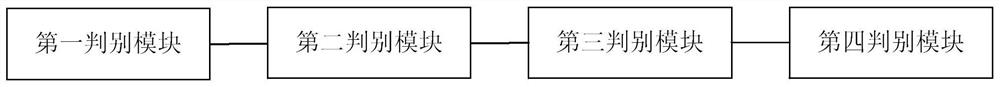
[0088] The embodiment of the present invention also proposes an authentication device to prevent the lock from being copied, such as image 3 shown, including:
[0089] The first judging module is used to judge whether the lock connected by the electronic key is a smart lock, and when it is judged that the connected lock is a smart lock (that is, the judgment result is "Yes"), the second judging module is notified to verify the communication received from the smart lock whether the key is correct;
[0090] The second judging module verifies whether the communication key received from the smart lock is correct, and when it is verified that the communication key received from the smart lock is correct (that is, the judgment result is "yes"), it notifies the third judging module to judge whether the communication key received from the smart lock is correct. Whether the type of smart lock is correct;
[0091] The third judging module is to judge whether the smart lock type recei...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com