Method and device for realizing virtual firewall
A technology of virtual firewall and configuration parameters, applied in the field of network security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0061] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0062] The invention provides a method for realizing a virtual firewall.
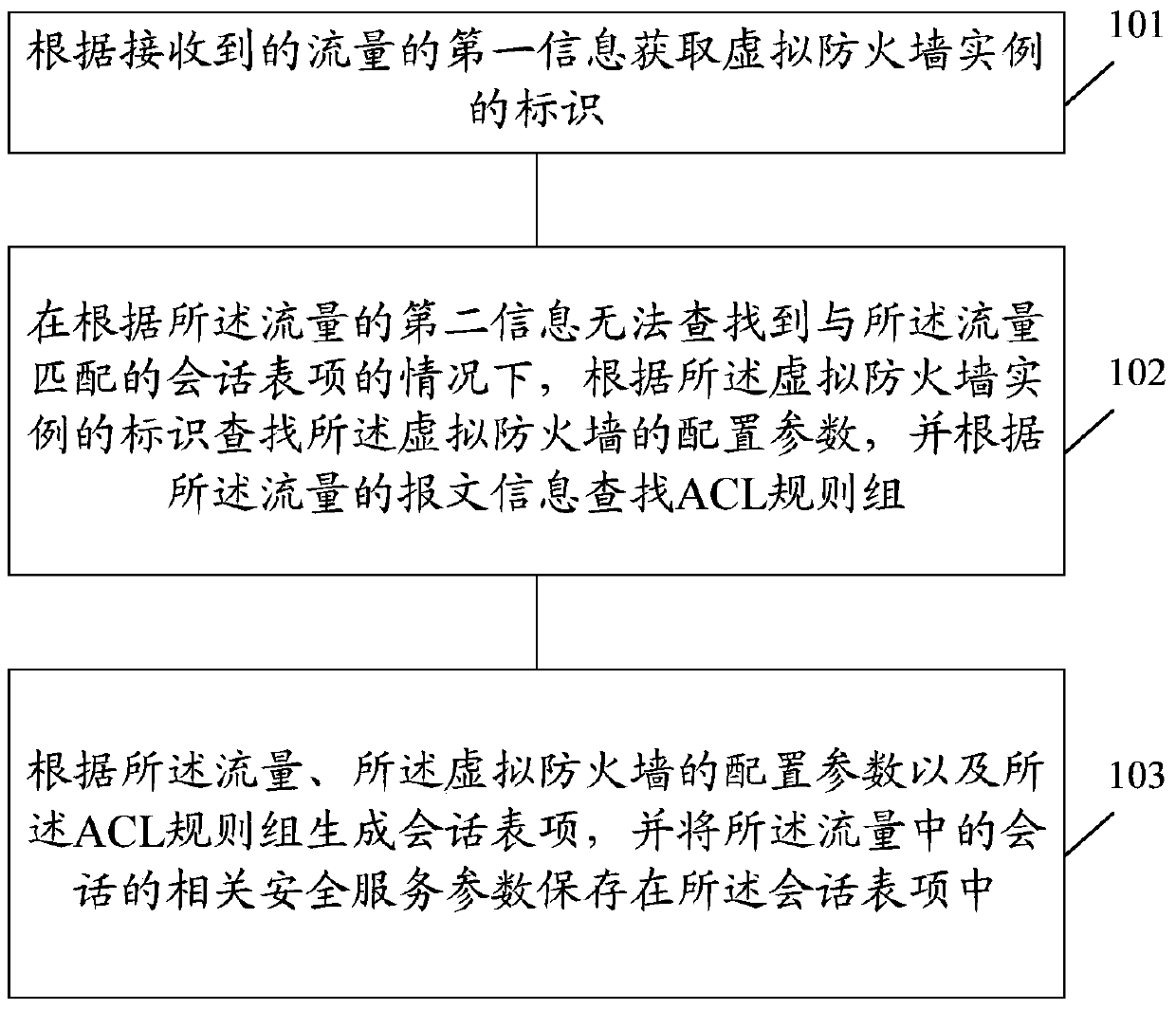
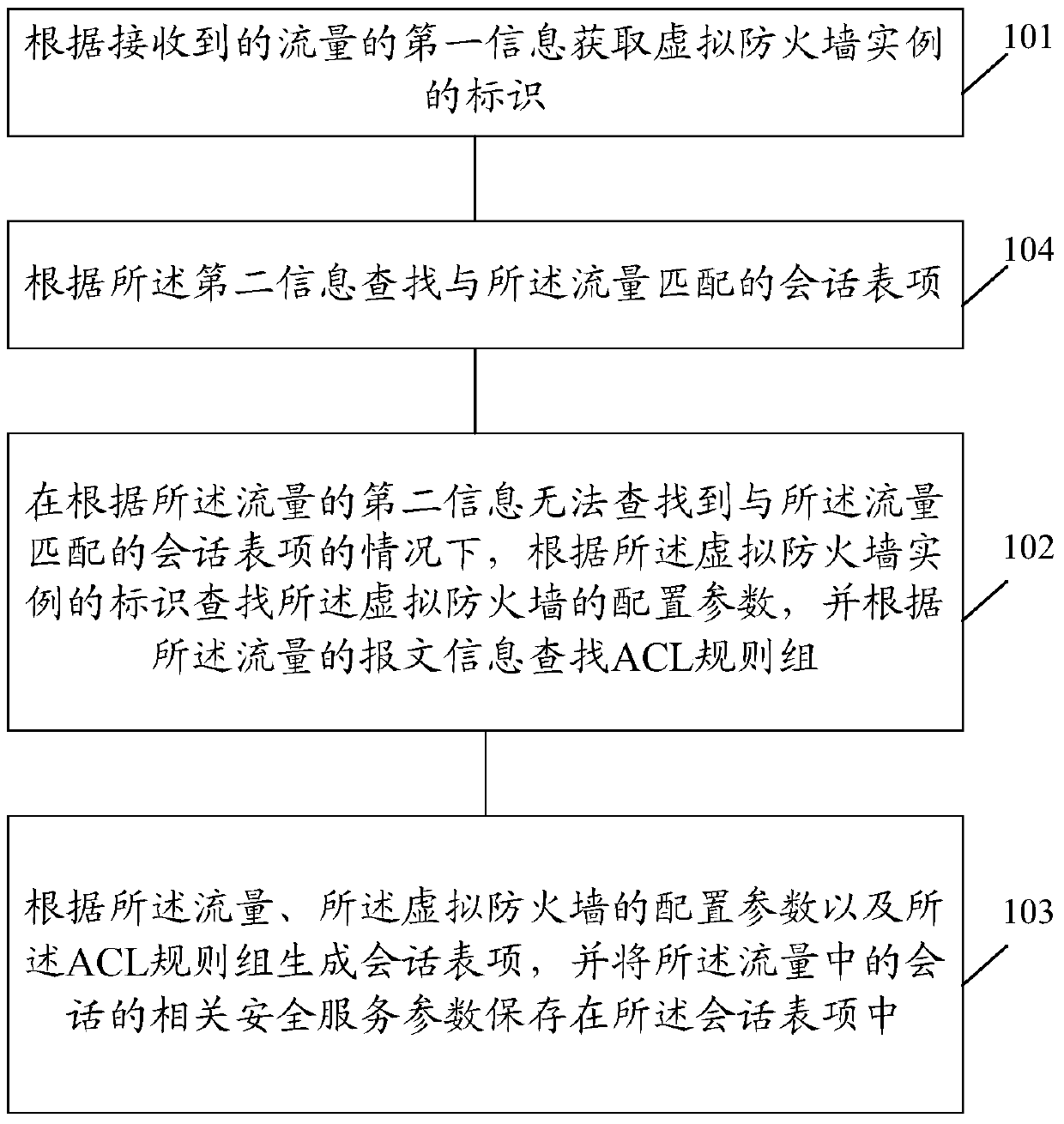
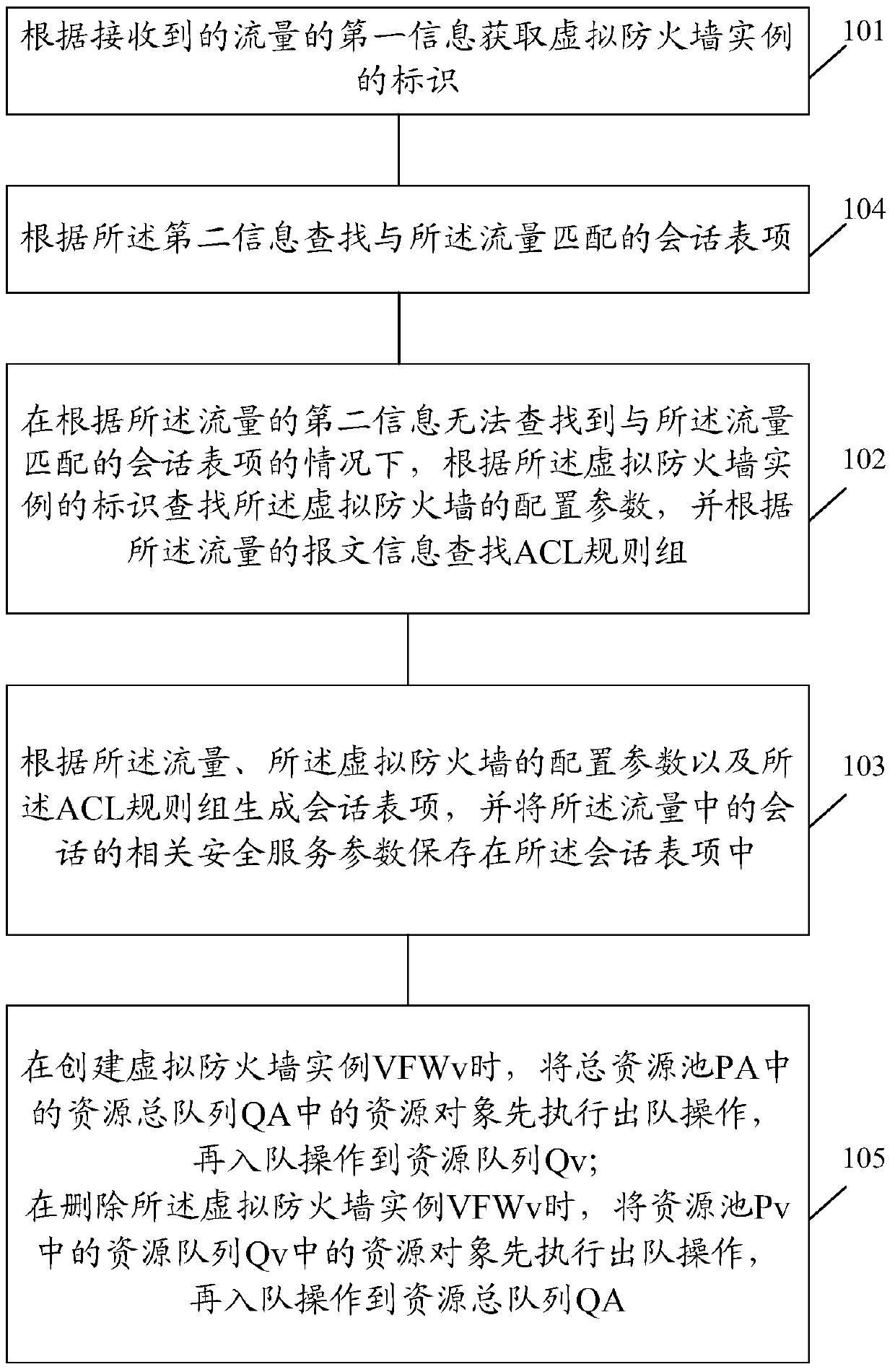
[0063] refer to figure 1 , figure 1 It is a schematic flowchart of the first embodiment of the method for implementing a virtual firewall in the present invention.
[0064] In the first embodiment, the method for implementing a virtual firewall includes:
[0065] Step 101, obtaining the identifier of the virtual firewall instance according to the first information of the received data flow;
[0066] Wherein, the first information includes at least quintuple, virtual local area network (Virtual Local Area Network, VLAN) information or Internet Protocol (Internet Protocol, IP) information in the packet of the data traffic.
[0067] Preferably, said obtaining the identifier of the virtual firewall instance according to the first information of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com