Re-encryption method, re-encryption system and re-encryption device
A technology for re-encrypting and encrypting keys, which is applied in transmission systems, electrical components, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
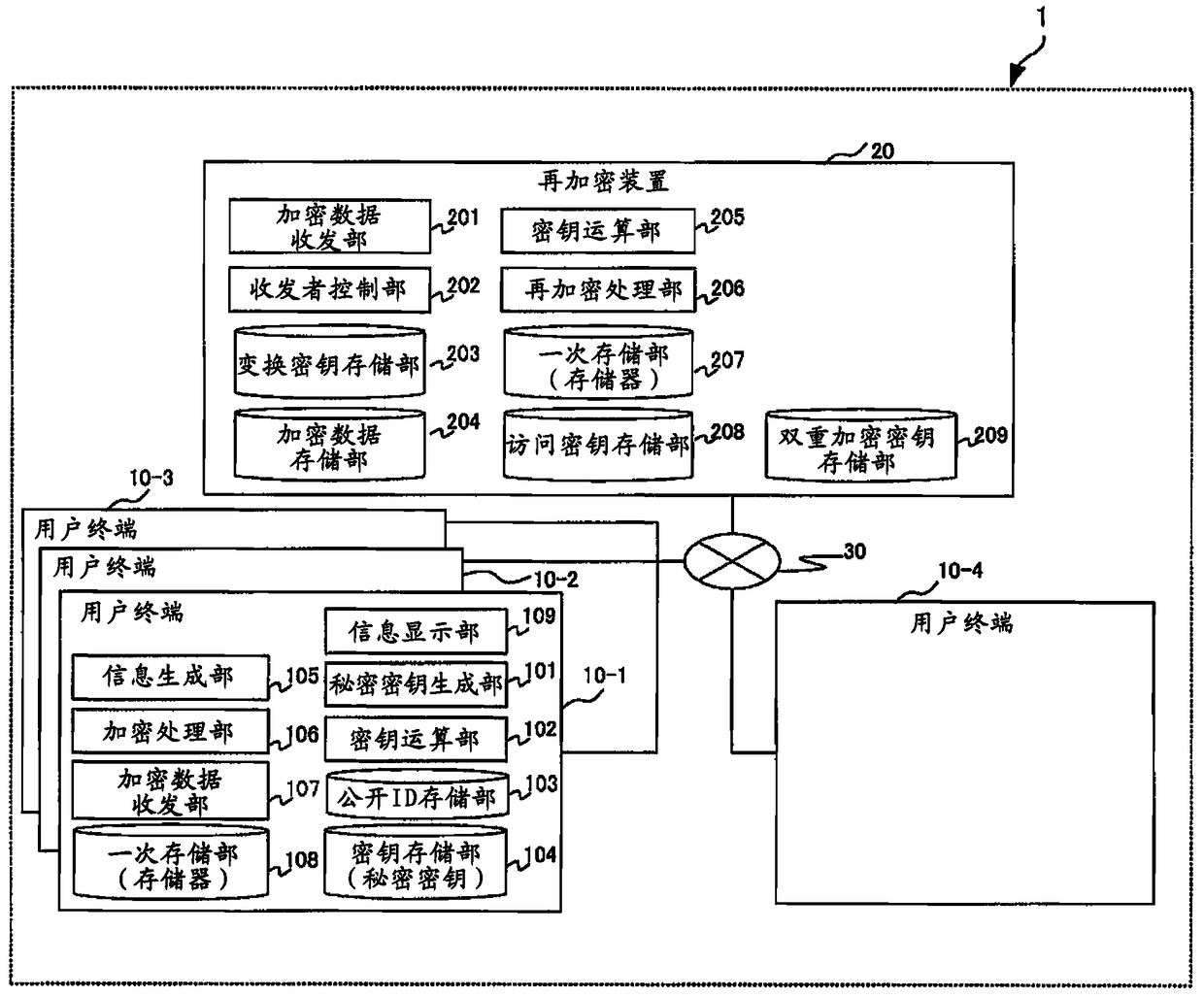
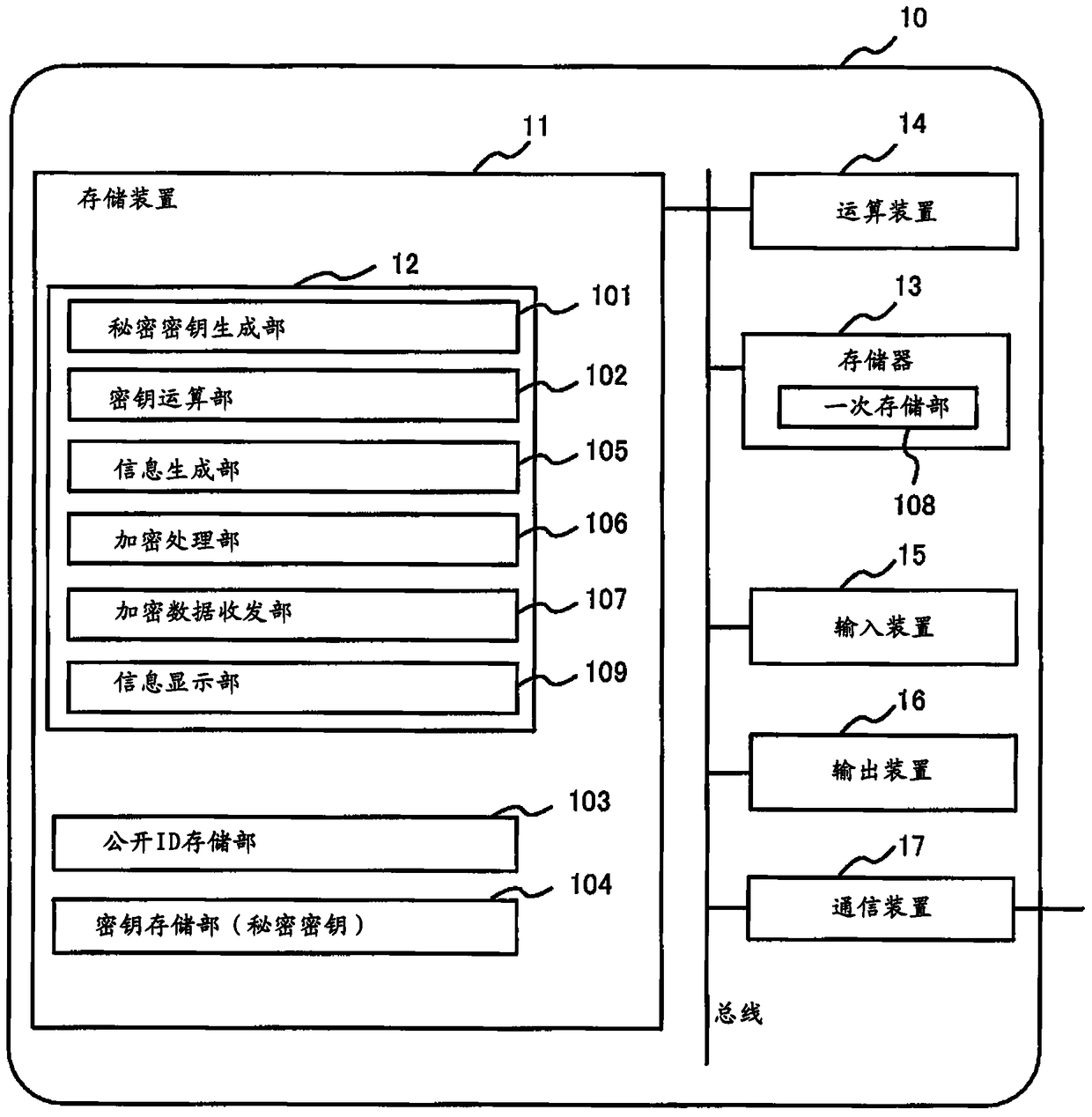
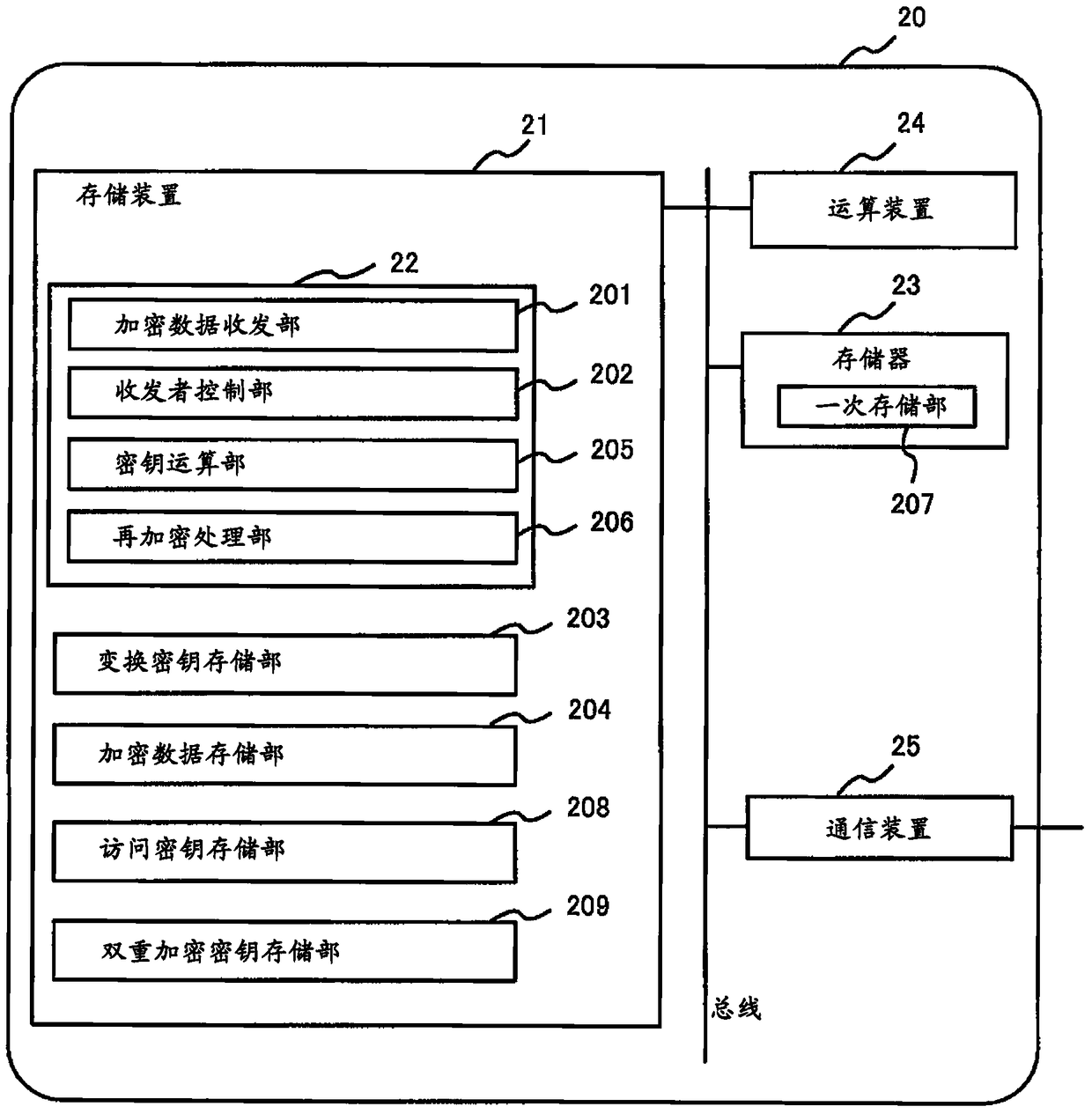
[0047] system structure
[0048] Hereinafter, embodiments of the present invention will be described in detail using the drawings. figure 1 It is a diagram showing an example of the overall configuration of the re-encryption system 1 including the re-encryption device 20 according to this embodiment. In this figure, an example of the functional configuration of each computer constituting the re-encryption system 1 is shown together with the overall configuration. figure 1 The shown re-encryption system 1 is in an environment in which the re-encryption device 20 (predetermined device) saves encrypted data shared among a plurality of users and manages the viewing authority of each user, so that the re-encryption device 20 is definitely avoided. A system where unauthorized persons including administrators can read encrypted data.
[0049] In the re-encryption system 1 of this embodiment, a plurality of user terminals 10 (in this embodiment, in order to distinguish between a plu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com