Methods and apparatus for anonymising user data by aggregation
A user data, user technology, applied in data processing applications, digital data protection, electrical digital data processing, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example
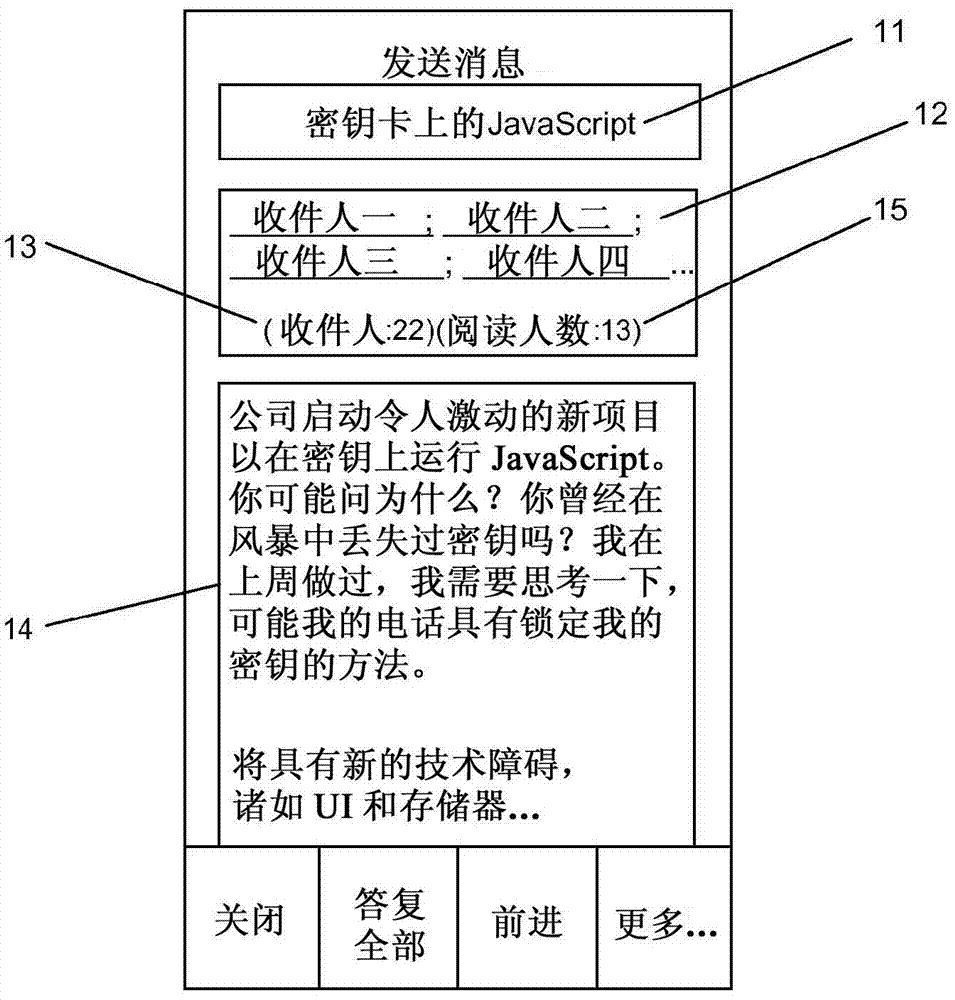
[0223] The example scenarios for the above requirements are as follows:
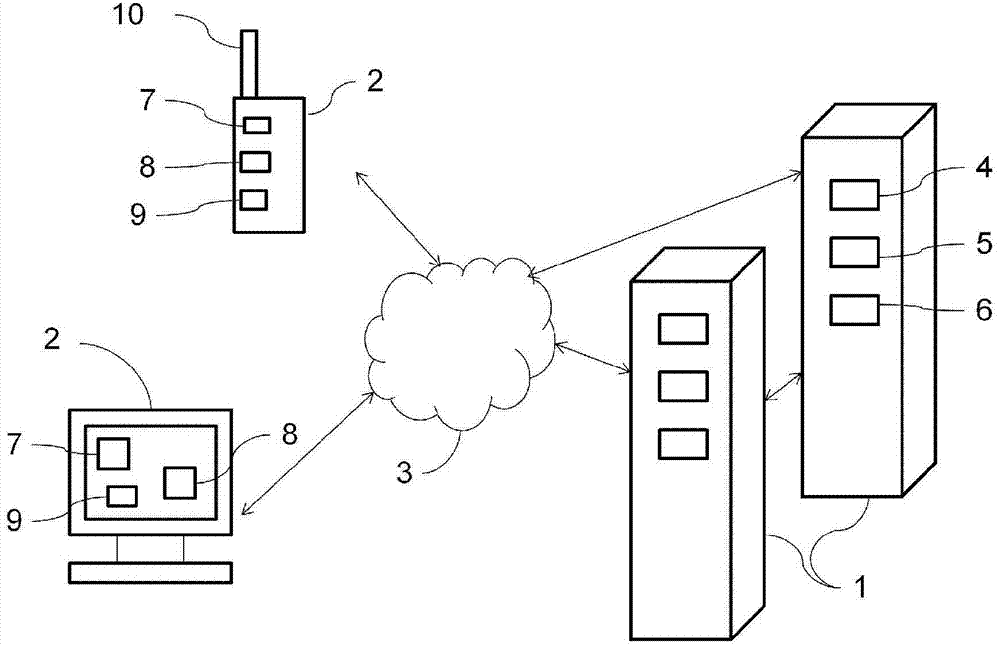
[0224] 1. There is a network of nodes, where a node is a computer that has access to event data about email messages in an email system. No node has access to all event data. Nodes generally do not share data to which they have access. (This describes a typical anonymous aggregation network, see above).
[0225] 2. A query is initiated on behalf of a user of the system to count how many recipients of an email message sent by the user have now read the message. (This is a typical anonymous aggregation command, see above).
[0226] 3. Each node in the network can perform a query about read events for the message in question. This gives each node a list of references to email users. In some or even all nodes the list may be empty.
[0227] 4. To complete the query, the list of each node now needs to be shared in the following way:
[0228] (i) There are no duplicate references on the shared list.
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com