Method for role-based access control model with precise access control strategy
An access control strategy and access control technology, applied in the field of security authorization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
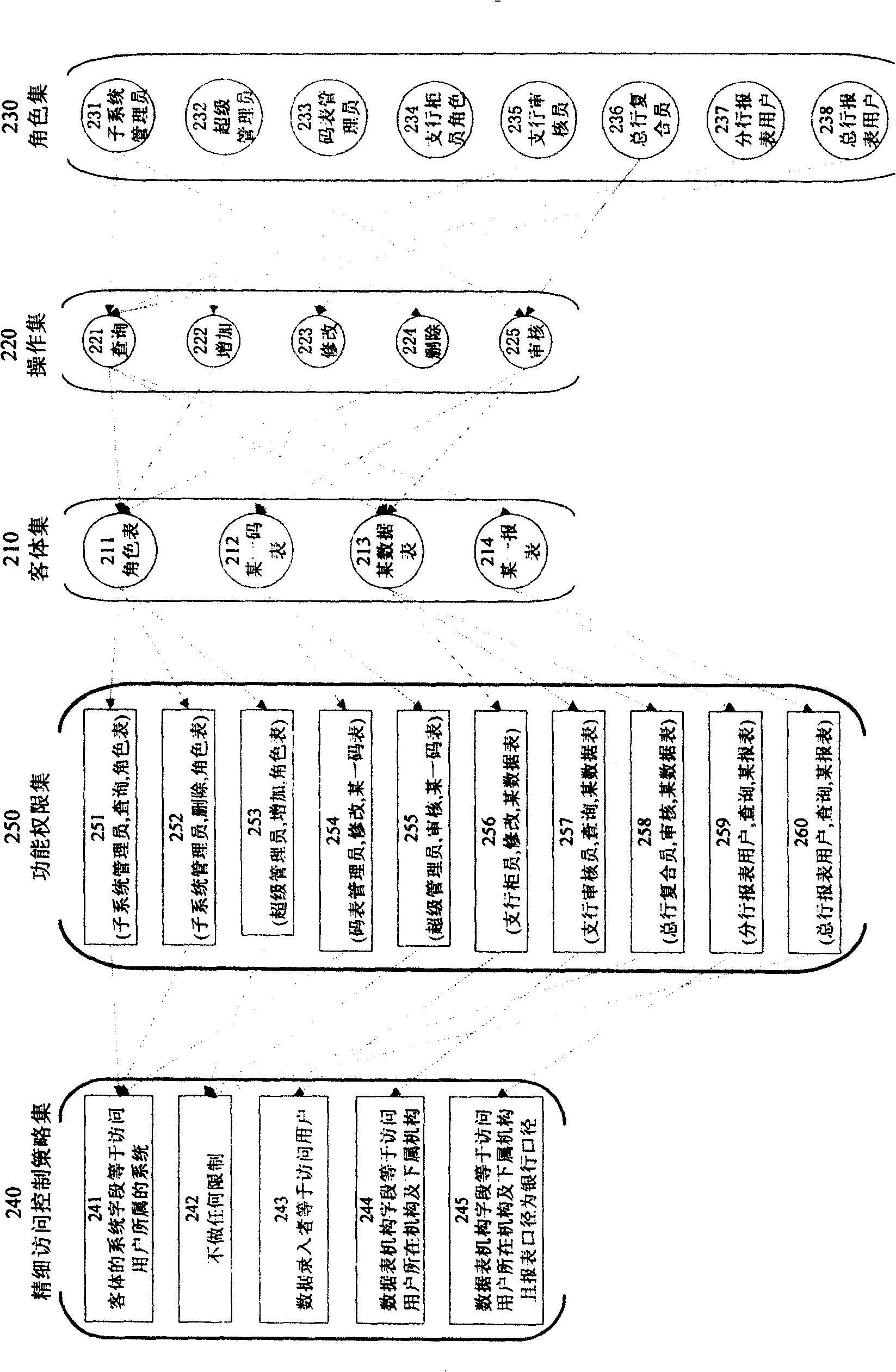
[0112] Example 2 as figure 2 Shown: the user is usually a system user, and the object is usually a database table, but not limited to this, the user can be a program, and the object can also be a data file, an XML file, or any computer resource, and the operations are not limited to the listed ones. It can be expanded arbitrarily according to the actual application system needs.
[0113] For example, in the management information system, the functional items are divided into four categories according to the coarse-grained division: system management, code table management, data processing and report query. It usually corresponds to four types of roles, that is, roles related to system management, roles related to meter management, roles related to data processing, and roles related to report query.
[0114] System management is used for adding, changing, reviewing, querying, system log monitoring, user locking and unlocking, etc. for users using the system. The roles involv...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com