Shilling attack detection method based on stack type sparse self-encoder
A sparse autoencoder and attack detection technology, which is applied in the field of information security, can solve problems such as difficult to deal with trust attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
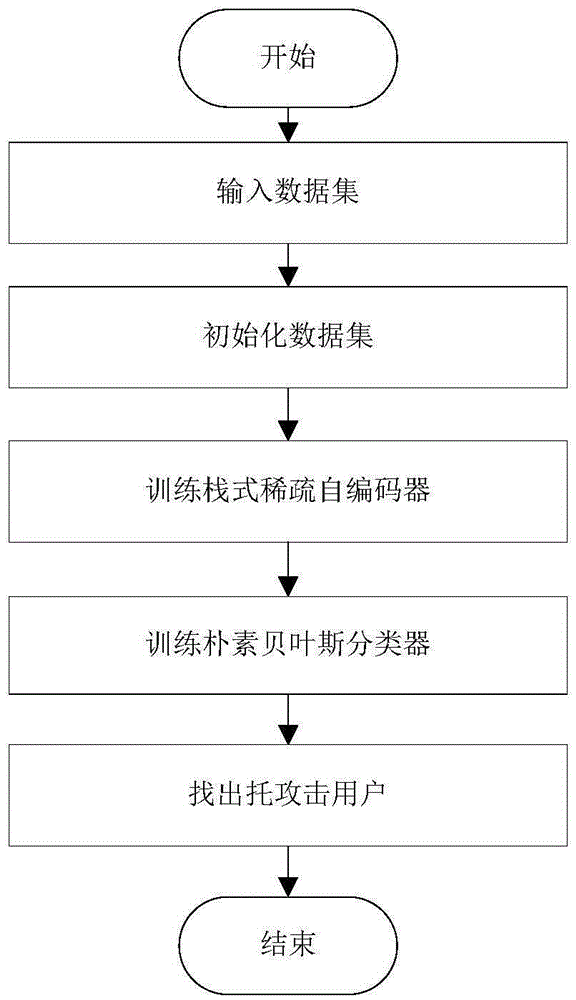
[0021] refer to figure 1 , the implementation steps of the present invention are as follows:
[0022] Step 1, input scoring dataset.
[0023] The scoring data set is divided into a large number of unknown types of users and a small number of known types of users, both of which include trusted users and normal users, and the entire scoring data is R=|D|×|I|, where R refers to the scale of The rating matrix of D|×|I|, D refers to all users, I refers to all items, |D| and |I| refer to the number of D and I respectively, and D=D U ∪D 1 ∪…∪D q ∪…∪D c , 1≤q≤c, where D U refers to a collection of users of unknown type, D q refers to the known set of q-type users, and c refers to the total number of known user types;
[0024] Step 2, normalize the scoring matrix R.
[0025] When users evaluate items, since the scoring scales of each user are different, for example, for their favorite items, some users will give full marks, while some users will only give average marks, which w...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com